Why it matters: Steganography is a technique for hiding data within images, and it is not new. However, it can be tricky to upload those images to services like Twitter while keeping the data intact. Twitter strips most of the metadata from images when you post them, making it hard to post more than just a little bit of data.
However, one researcher noticed that tweets would leave one form of metadata alone. So with a little coding ingenuity, David Buchanan was able to cram the entire works of Shakespeare into one tiny image and post it in a tweet.
Assuming this all works out, the image in this tweet is also a valid ZIP archive, containing a multipart RAR archive, containing the complete works of Shakespeare.
— Dаvіd Вucһаnаn (@David3141593) October 29, 2018
This technique also survives twitter's thumbnailer :P pic.twitter.com/P0Owq9abRC
Buchanan told Motherboard that Twitter does not touch a particular type of image metadata called ICC.
“So basically, I wrote a script which parses a JPG file and inserts a big blob of ICC metadata,” Buchanan said. “The metadata is carefully crafted so that all the required ZIP headers are in the right place.”
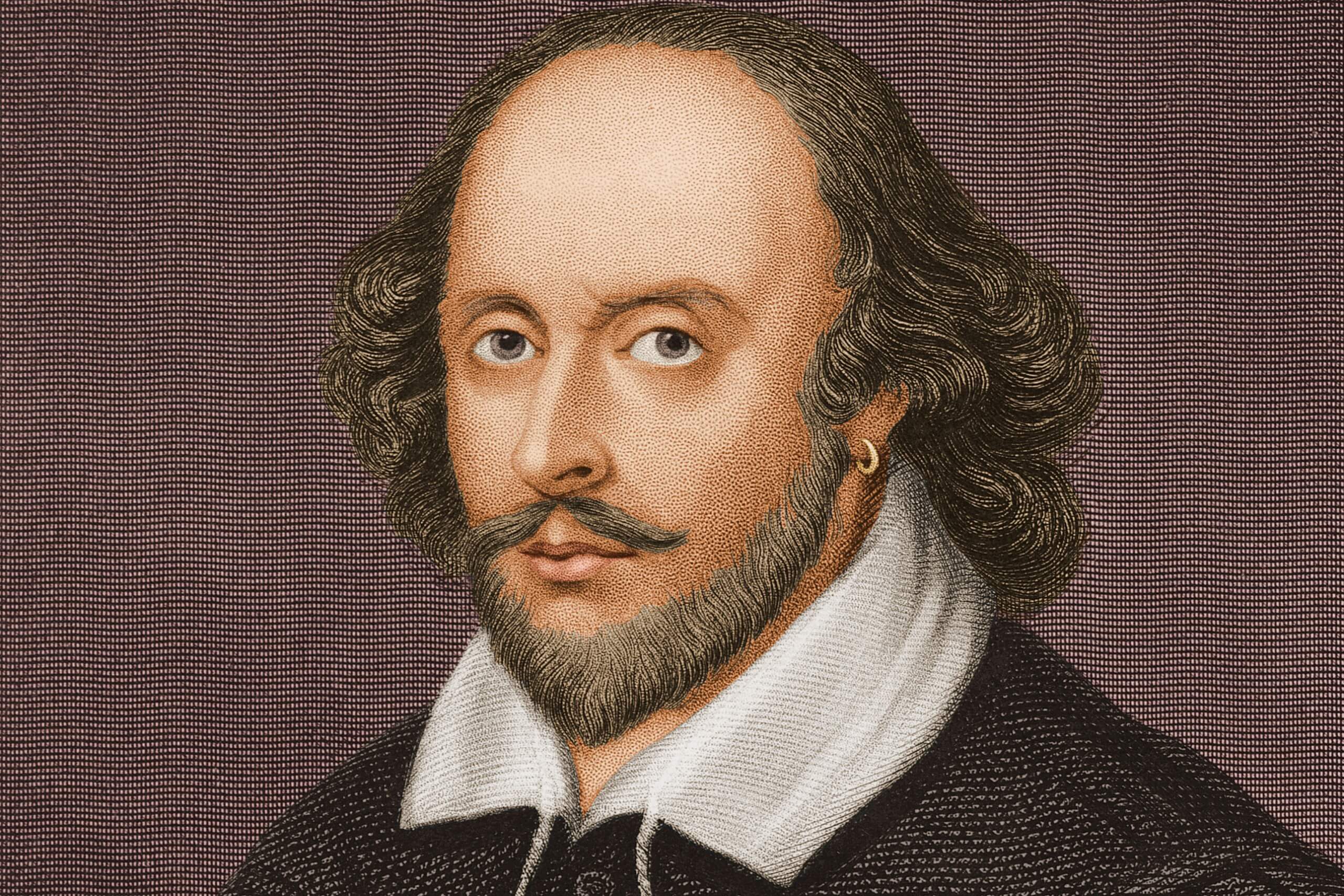
He noted that the process is not perfect and requires a lot of “fiddling.” It took him two hours to get all the compressed data into the image that is, appropriately, a low-res portrait of Shakespeare that says, “Unzip Me.”
"I tried reporting this techinque to twitter's bug bounty program, but it's #notabug."
Buchanan said he got the idea while he was trying to see how much raw data he could stuff into one tweet.
“A while later I had the idea to embed a ZIP file,” he said
After finding the tweet had successfully posted, Buchanan replied with instructions on how to extract the data. Followers were able to confirm that the files are all intact and contain the works as found in Project Gutenberg.
He acknowledges that the technique presents an opportunity for bad actors to distribute malware, but says this use case has already been employed, just with smaller packages.
“[Malware distribution] already has been possible via more ‘traditional’ steganography techniques, but this method allows you to pack in way more data.”
I tried reporting this techinque to twitter's bug bounty program, but it's #notabug. Fair enough, but that just means we can have some fun with it
— Dаvіd Вucһаnаn (@David3141593) October 29, 2018
Buchanan said that he tried to collect a bug bounty from Twitter for the exploit, but was denied. Twitter told him it was not a bug. “Fair enough, but that just means we can have some fun with it,” he tweeted.
Steganography has also been used to secretly pass messages over social media. A browser extension called "Secretbook" allows users to embed a 140-character message with a password into an image and upload it to Facebook. Only those with the password can extract the message.
https://www.techspot.com/news/77209-someone-tweeted-entire-works-shakespeare-one-tweet.html