
Security is hard but you'd at least expect some level of protection to be made when dealing with top-secret military intelligence. Unfortunately, it appears that this wasn't exactly the case for some data shared between the US Army and the NSA. Security firm UpGuard has discovered a publicly accessible AWS S3 bucket that contains classified information on the Distributed Common Ground System - Army as well as details of communications with federal IT environments.
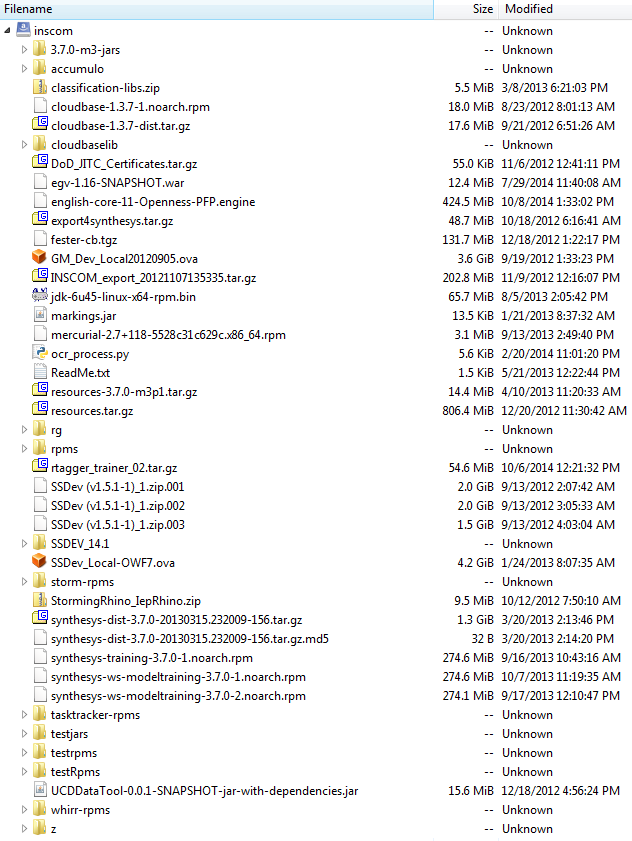
The discovery was actually made back in September but has just now been made public. Among the 47 viewable files in the bucket were details of a cloud-based program called Red Disk. This program was developed in haste to better deliver intelligence to troops through the use of laptops and tablets. It was never formally finished and many have viewed it as defense contractors siphoning off money from the military in times of emergency.
The information publicly available also included a virtual hard drive with files classified as NOFORN. That means its details are so secretive that not even US allies can view it. Thankfully, most of the data can't actually be viewed without connecting to the Pentagon's internal network. It did, however, contain encryption keys and hashed passwords used by former contractors.
This isn't the first time top-secret information has been inadvertently made public online as UpGuard discovered a similar case a while back. While this was likely just a simple misconfiguration of the privacy settings and permissions, the researchers view it as a symptom of a much bigger problem.
They concluded that "given how simple the immediate solution to such an ill-conceived configuration is—simply update the S3 bucket’s permission settings to only allow authorized administrators access—the real question is, 'how can government agencies keep track of all their data and ensure they are correctly configured and secured?'." It's a question that is not easily answered.
https://www.techspot.com/news/72082-top-secret-us-army-intelligence-accidentally-posted-public.html