Your Apple notebook might be vulnerable to an attack that could cause its battery to die, harbor malware or even explode, according to security researcher Charlie Miller. Speaking with Forbes, Miller explained that modern laptop batteries contain a controller that monitors their power level and regulates when they start and stop charging. After examining various MacBook, MacBook Pro and MacBook Air batteries, he found a way to manipulate the chip to cause some disastrous effects.
The batteries ship with a default password that restricts access to the controller's firmware, but that can be bypassed fairly easily. Miller discovered two of Apple's battery passwords by dissecting a 2009 software update released to fix a glitch with MacBook batteries. With those keys in hand, he managed to reverse engineer the controller's firmware, allowing him to reprogram the chip so it reports the wrong readings and eventually burns itself out – be that figuratively or literally.
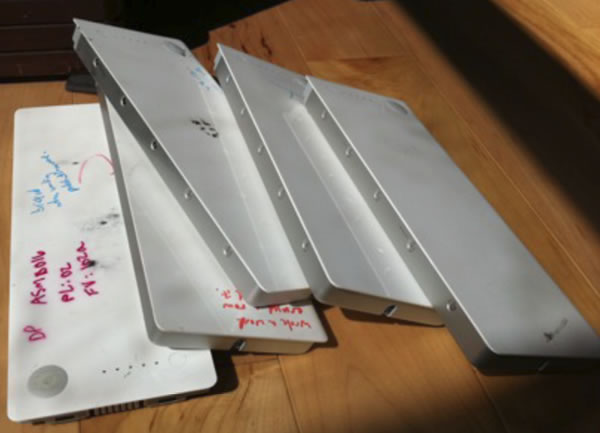
Batteries slain by Miller's hand
Potentially more startling than a flaming battery, an attacker could infect the firmware with malware, allowing them to harvest the victim's personal data. Miller noted that it would be especially nasty because few IT professionals would consider the battery as a source for the malware, allowing it to reinfect the machine perpetually. Someone could install a new hard drive, a fresh operating system, flash the system's BIOS and the malware-laden battery would live on to reattack the machine.
During his research, Miller claims to have bricked seven batteries, but he didn't attempt to push them far enough to catch fire because he works at home. "You read stories about batteries in electronic devices that blow up without any interference. If you have all this control, you can probably do it," he said. Miller will demonstrate the flaw during next month's Black Hat conference along with releasing a tool for MacBook users called "Caulkgun" that changes the battery's default password.