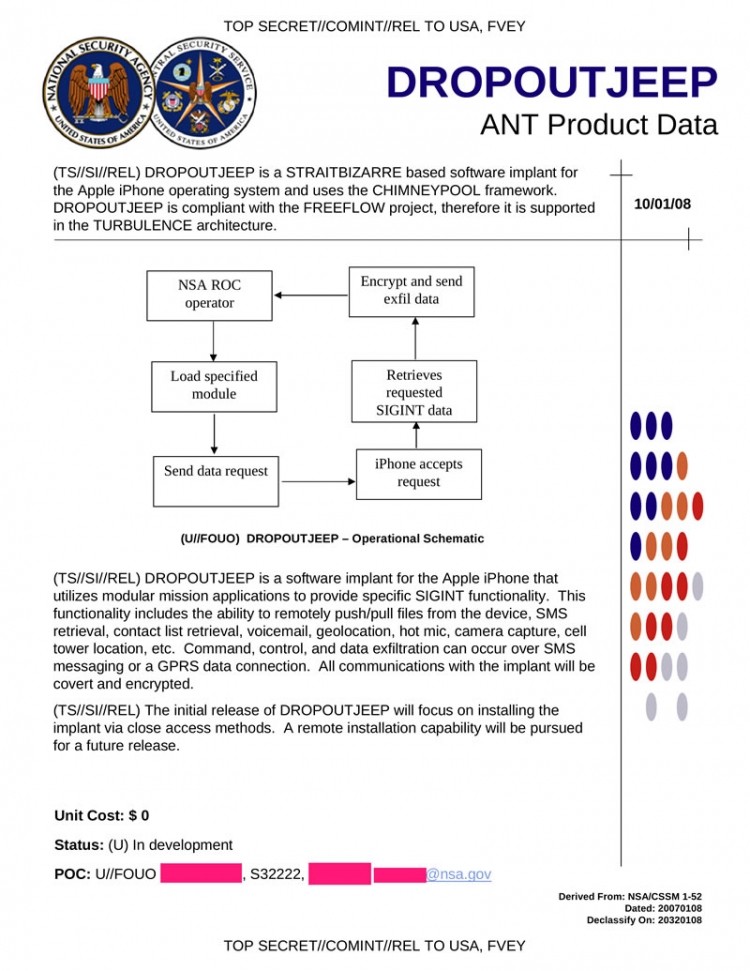
The National Security Agency developed a program in 2008 that allows them to access nearly everything stored on an iPhone according to security researcher Jacob Applebaum and German news magazine Der Spiegel. Known as DROPOUTJEEP in a leaked document from late 2008, the program lets the agency intercept SMS messages, access contact lists, locate a phone using cell tower data and even remotely activate a phone's camera and microphone.
Even more chilling, the NSA claims a 100 percent success rate when implanting an iPhone with the spyware although physical access to the handset is needed for installation. The German news magazine suggests special NSA Tailored Access Operations teams may have intercepted device shipments, opened and installed the software then sent them along to the end user.
Given how careless some people are with their phones, however, it probably wouldn't be too difficult of a task for an undercover agent to perform the implant post-delivery, but I digress.
The leaked document also said a remote installation method would be pursued for a future release.
When asked about the program at the Chaos Communications Congress in Hamburg, Germany, Applebaum said either the NSA has a huge collection of exploits that work against Apple products or Apple sabotaged it themselves. When pressed further about if he thought Apple helped the NSA, he said he hoped Cupertino would clarify.
It's been more than five years since the purported leaked document was written. As such, we have no idea if the NSA moved forward with the program and if they did, how many infected iPhones are in the wild.