The FBI has decided that it doesn't need to reveal how it unlocked the San Bernardino iPhone, which will prevent Apple from identifying the security vulnerability and closing it through a software update.
Under a rule brought in by the US government in 2010 called the "Vulnerabilities Equities Process", government agencies like the FBI have to disclose any back doors or flaws in technology that they discover. The idea is that these vulnerabilities would be disclosed in private to the companies who make the products, provided the National Security Council gives the all clear, allowing them to fix the issue and keep Americans safe.
However in the San Bernardino iPhone case, the FBI has a convenient excuse they can use to avoid disclosing the details of the vulnerability. As the agency used a third-party tool to unlock the device in question, the FBI can and will simply say that they are unfamiliar with how the tool works.
If the FBI claims it doesn't know how the tool works, they won't have to disclose to Apple or the National Security Council what vulnerability the tool used to bypass the iPhone's lock screen. This keeps the flaw open and would allow the FBI to use the same tool to unlock similar phones in the future if need be.
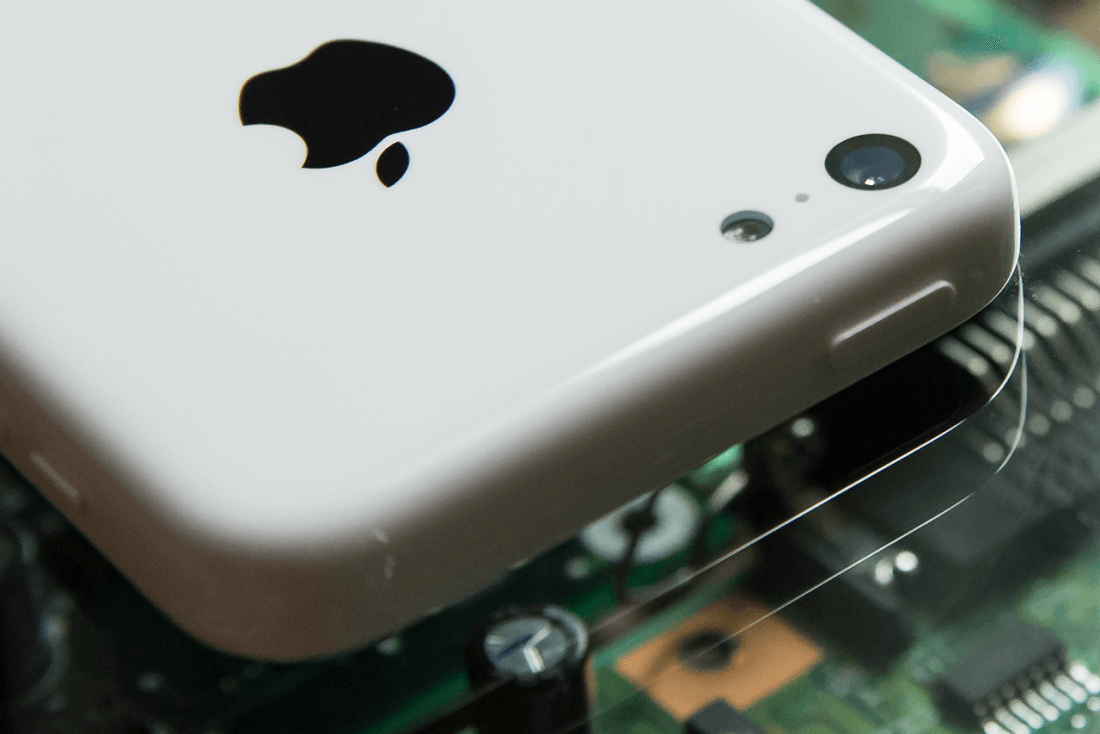
Apple no doubt will be annoyed at the FBI's refusal to detail which vulnerability allowed them to bypass the security measures on their handset. Although it's believed that the vulnerability is not present in more modern devices (the San Bernardino killer used an old iPhone 5c), Apple still wants to keep their entire product portfolio secure.