With the promise of high returns on investments, more people are buying into the huge number of altcoins that are appearing. Now, hackers are taking advantage of this practice through a type of ransomware that pretends to be a new cryptocurrency wallet but instead locks down a victim's computer.
Researchers from Fortinet's FortiGuard Labs discovered the fake cryptocurrency "written in JavaScript," which is called "SpriteCoin." It attempts to draw people in by promising that it is "sure to be a profitable coin" for investors.
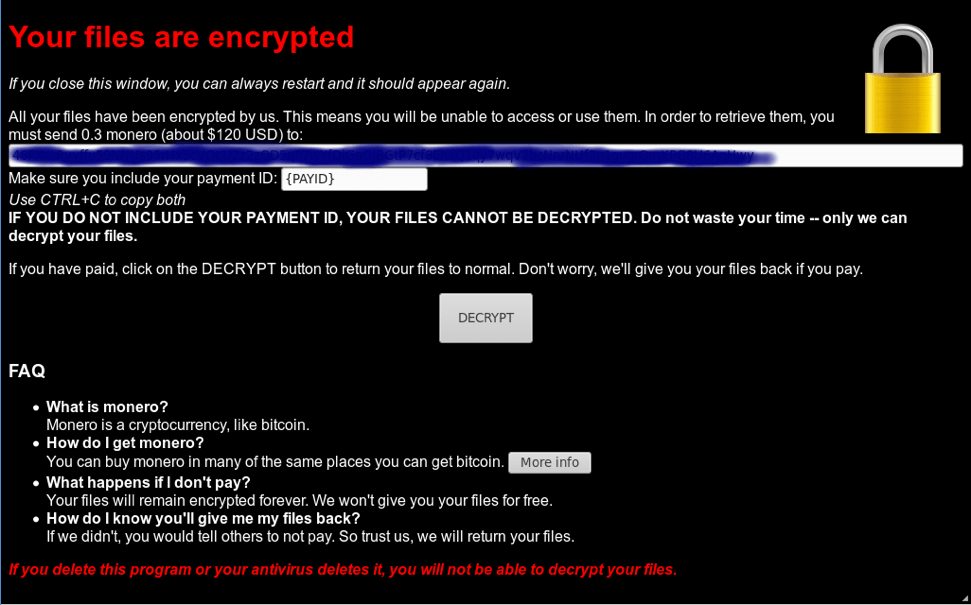
Once someone downloads the executable file, the person is asked to enter a wallet password and notified that it is downloading the blockchain. In reality, a file called MoneroPayAgent.exe is downloaded, which encrypts the PC's files. Once the ransomware takes hold, it demands a payment of 0.3 Monero, currently worth just under $100, for the decryption key.
As if the encryption isn't bad enough, the victim's Chrome and Firefox credentials are harvested and stored using an embedded SQLite engine and transmitted to the attackers' Tor website via POST requests, which could give the hackers access to a user's passwords.
Ransomware victims are usually advised not pay the demands, and in this case that's good advice to follow. Should someone hand over the Monero, they'll be infected with another piece of malware called W32/Generic!tr, which can activate device cameras, harvest certificates, and parse keys. The researchers write that paying the ransom "leaves the victim more compromised than before."
"The allure of quick wealth through cryptocurrency seems to be enough to trick unsuspecting users to rush toward the wallet app du jour without consideration," wrote the FortiGuard SE Team.
It's thought that those behind SpriteCoin aren't in it for the money or the stolen user credentials.
"What we infer is that the intent is not about the amount of money, but possibly about proof of concept or testing new delivery mechanisms, and to see how many people would fall for it," senior security researcher at Fortinet, Tony Giandomenico, told ZDNet.
