IBM has implemented a complete ban on the use of removable storage devices to prevent the accidental spread of malware and theft of data.
Curiosity is one aspect of human nature that is difficult to suppress all in the name of corporate security. There have been numerous cases in the past where flash drives are picked up outside and then plugged in to corporate computers that are then infected.
Back in 2010, Avast put out a warning that the majority of malware in existence is capable of being spread by USB drives. Since then, developers of malicious software have only gotten more creative about how to hide their payloads on removable devices.
IBM has already banned the use of removable storage devices in certain divisions where security is tight, but is now expanding the policy globally. Instead of using removable storage, employees are being directed to use a file sync 'n' share service for sending and receiving data.
Management is reportedly aware that the new policy could be "disruptive for some," but believes that the minor inconveniences far outweigh "the possible financial and reputational damage from misplaced, lost or misused removable portable storage devices must be minimized."
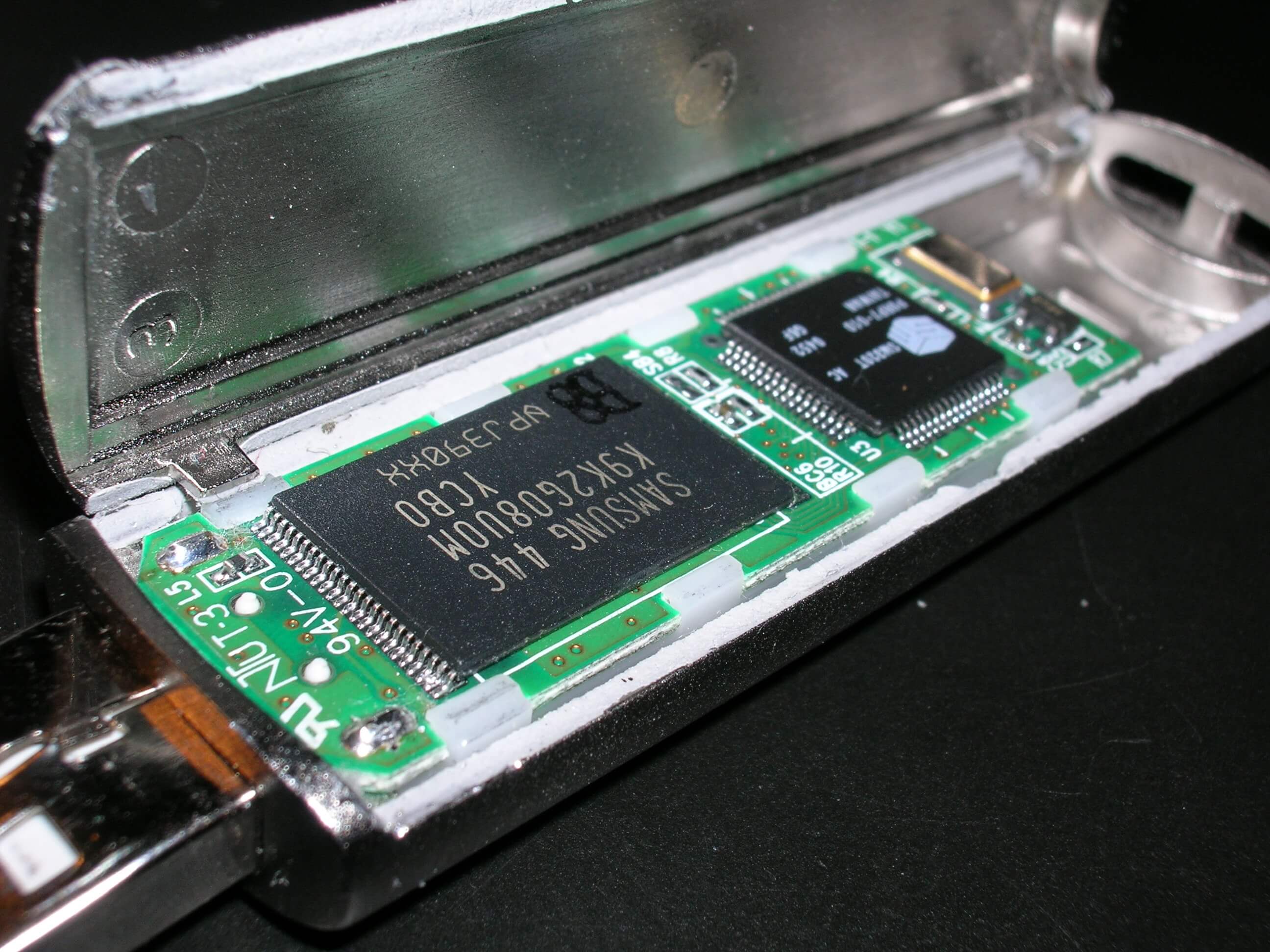
Even with AutoRun features disabled, USB devices can still be disguised as flash drives but appear as human input devices such as mice and keyboards. Using a microcontroller embedded in a specially crafted USB stick, keystrokes and mouse clicks can be automatically sent to any machine where USB ports are enabled.
Human input devices do not require any special authorization to begin functioning on modern operating systems. This is a known vulnerability, but with no obvious solution available. If actions are required to enable a mouse and keyboard, how would that be done if there is no way to input a choice?
