Scorpion says: "Get over here!" Watch out for emails from the crypto exchange CoinPayments. Hackers are running a new "Mortal Kombat" ransomware campaign. The attackers disguise the phishing email attachment to look like payment transactions. However, when opened, the payload automatically downloads either ransomware or a crypto-wallet skimmer. So it's a bit like a one-two uppercut. TOASTY!
Security researchers from Cisco's Talos cybersecurity team have tracked a new ransomware campaign that uses images from Mortal Kombat in its ransom notes. The attacks started appearing in December and indiscriminately target individuals, small businesses, and large corporations.
Once infected, the affected computer displays a Mortal Kombat 11 wallpaper attached to a note instructing the victim to contact the attackers via an instant messaging app called qTox that anyone can download from GitHub. The attackers will then negotiate a price to be paid in Bitcoin.
The attack vector is phishing emails made to look like they are from the crypto trading platform CoinPayments. The emails claim that the user's payment has "timed out." An attachment carries the payload in a zipped file with a name that looks like a CoinPayments transaction number. When opened, it downloads the Mortal Kombat ransomware.
The ransomware will encrypt all files on the victim's PC, including those in the trash bin and virtual machine files. It also corrupts Windows Explorer, deletes folders and files from the startup menu, and disables the Run command. However, it doesn't display any wiper capabilities or erase volume shadow copies in the computer.
Talos notes that the email attachment may alternatively download Laplas Clipper. This malware monitors the computer's clipboard for cryptocurrency wallet addresses. If it finds one, it sends it to the attacker's server, where a "Clipper bot" creates a "lookalike" address owned by the hacker and then replaces the clipboard entry. Users then unknowingly transfer funds into the hacker's wallet instead of their own.
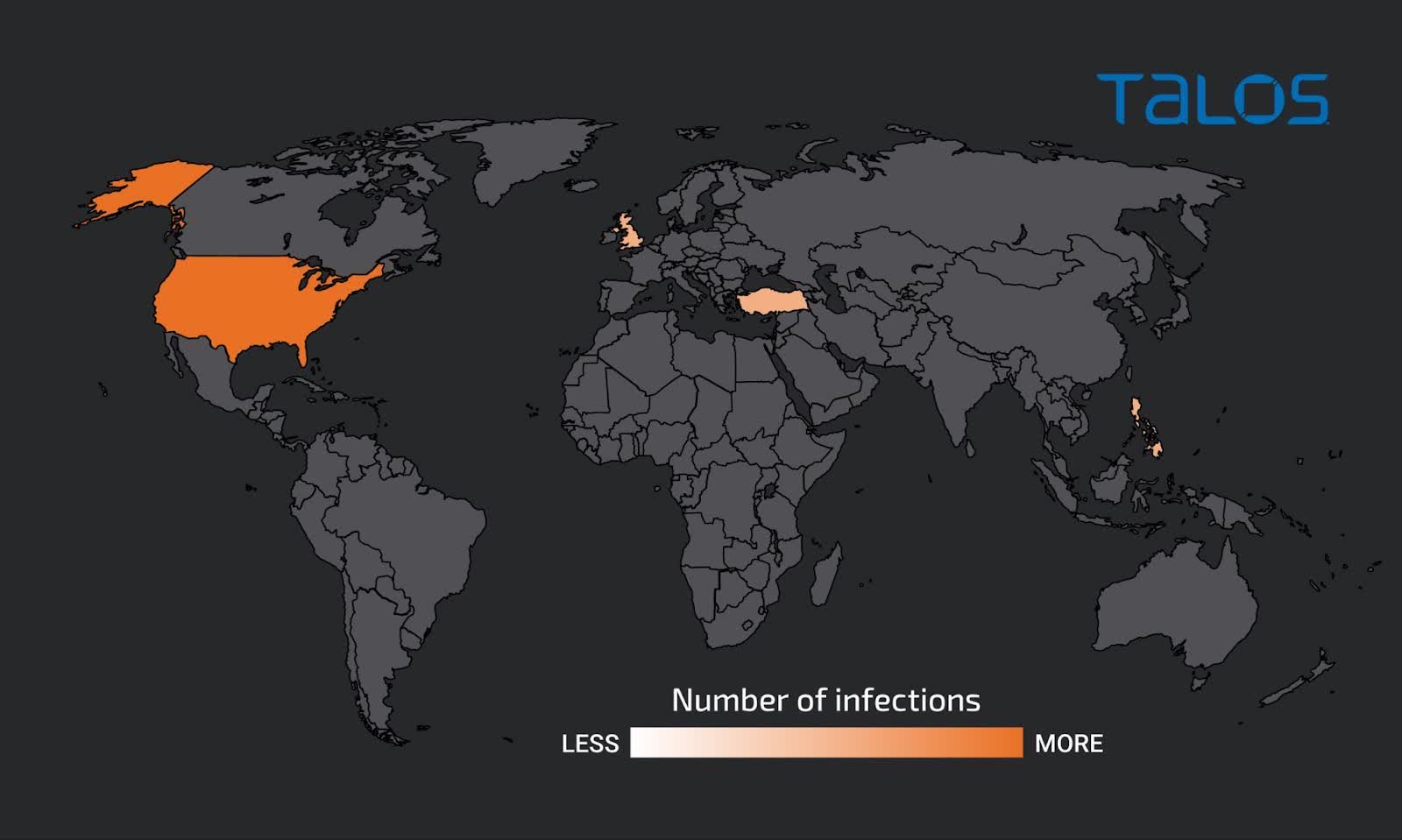
Talos says that although the Mortal Kombat ransomware is new, it appears to be a Xorist variant. Xorist dates back to at least 2010. The researchers tracked attacks, and most seem confined to the United States, with a light scattering of victims in England, Turkey, and the Philippines.
As always, the best mitigation for ransomware attacks is to remain vigilant and suspicious of random emails from services you use. Watch out for attachments or requests for your credentials. Companies rarely send customers files or ask for usernames or passwords.
