In a nutshell: The Flipper Zero may look like a harmless child's toy from the 90s, but it's capable of far more. The Tamagotchi-like device has been used for everything from opening parking gates and tampering with fast food menus to reading credit card information through a person's wallet and pants. Unfortunately for Flipper, this scanning ability has earned a ban from Amazon, which now considers it a policy-breaking card-skimming device.
The device allows users to locate, troubleshoot, test, and debug different types of digital interfaces and hardware devices via radio, radio frequency identification (RFID), near field communication (NFC), infrared, Bluetooth, and other protocols. While these options aren't inherently dangerous on their own, the ability to emulate multiple devices, cards, or interfaces is what many see as one of Flipper's several security threats.
The ability to read and emulate NFC data means that cards or devices in proximity and broadcasting on the 13.56 MHz band could be read and potentially emulated (to the extent possible) without the owner's knowledge.
Based on this capability, Amazon sees the Flipper Zero's NFC capabilities as a potential policy-breaking security risk, as many bank and credit cards that offer contactless transactions utilize NFC communication. The capability qualifies the Flipper Zero as a restricted card-skimming device under the Amazon Seller's Lock Picking & Theft Devices product category.
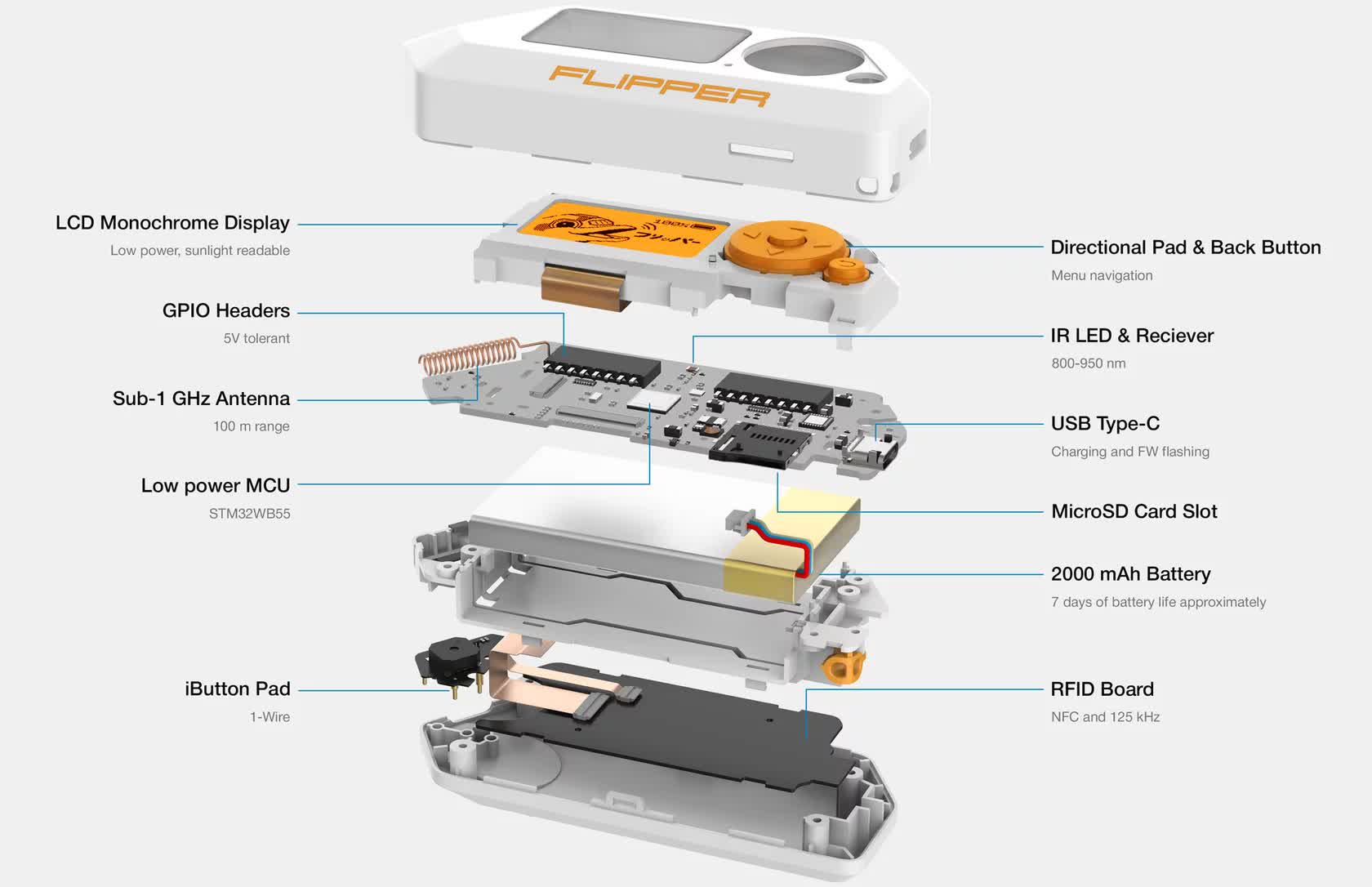
The Flipper Zero project was funded through a Kickstarter campaign in 2020. Some of the tech specs highlights include:
- 32-bit Arm Cortex-M4 processor + Cortex-M0+ 32 MHz (network)
- 1 MB of Flash memory and 192 KB of SRAM
- 1.4-inch 128 x 64 LCD monochrome display, 5-button joystick with back button
- 2000 mAh rechargeable battery
- NFC and Infrared
- RFID reader and writer, GPIO pins
- iButton reader and writer
- USB 2.0 port, type C
Despite this ability to read and emulate NFC data, the odds of a user actually cloning all required meaningful data from an unsuspecting victim's credit card is currently impossible. While the Flipper has the ability to read any unencrypted NFC data that exists on the card, it lacks any ability to read the additional encrypted data required to complete a transaction. Based on this, it is (currently) not possible for the Flipper Zero to 100% emulate a bank or credit card that uses NFC.
In a previous interview with Wired, Flipper Zero co-creator Alex Kulagin defended the device, stating that it is intended for educational purposes and hobbyists' entertainment. "We want to help you understand something deeply, explore how it works, and explore the wireless world that's all around you but difficult to understand," said Kulagin.
Since the ban, Amazon has instructed sellers to remove or delete any listings associated with the Flipper Zero or other restricted products. Sellers that fail to comply within 48 hours of receiving their warning face potential seller account cancellation, and their funds may be permanently withheld.
While there is no shortage of YouTube videos and other articles that focus on the Flipper's more "colorful" uses, the truth is that it was never originally designed with mayhem in mind.
The multi-antenna device is designed to assist security and other technical professionals in penetration testing, debugging, and other tasks intended to make products or services more stable and secure. But like any device, it's only as good or bad as the person using it. According to Kulagain, "that is not Flipper's fault. There are bad people out there, and they can do bad stuff with any computer. We aren't intending to break laws."
