In brief: A recently discovered security vulnerability impacting select Intel CPUs released between 2015 and 2019 has been patched thanks to a new software-level microcode update. Unfortunately, early testing has revealed some pretty significant performance penalties introduced by the mitigation effort.
Rob published a comprehensive report on Downfall yesterday. For the sake of brevity, I'll simply direct you to his article should you need to get up to speed on the vulnerability. Intel also has a list of affected processors.
Michael Larabel from Phoronix has put the microcode update to the test using a variety of processors including a pair of Xeon Platinum 8380 chips, a Xeon Gold 6226R, and a Core i7-1165G7 across multiple workloads in Linux.
The dual Xeon Platinum 8380 chips were about six percent slower in OpenVKL 1.3.1 but closer to 34 percent in some OSPRay 2.12 tests. In Neural Magic DeepSparse 1.5, the performance penalty reached nearly 21 percent in one test.
It's more of the same with the Xeon Gold 6226R CPU. In OSPRay 2.12, the performance hit in some instances was more than 32 percent, and in Neural Magic, up to 26 percent in one instance. Only a few tests were run on the Core i7-1165G7, with the performance impact ranging from 11.25 percent on the low end to around 39 percent on the high side.

The good news is that even in the worst case, the overhead wasn't as high as the 50 percent Intel said could be experienced in some instances.
It's worth noting that there is an opt-out mechanism in the microcode that allows users to disable the mitigation should they deem the performance hit too steep or don't believe they operate in an environment where they'd be susceptible to an attack. As Tom's Hardware notes, the complexity of the attack could also play into your decision on whether or not to bypass the mitigation.
Phoronix promised to explore additional workloads but as a one-man show, it's going to take Larabel some more time to get those results online.
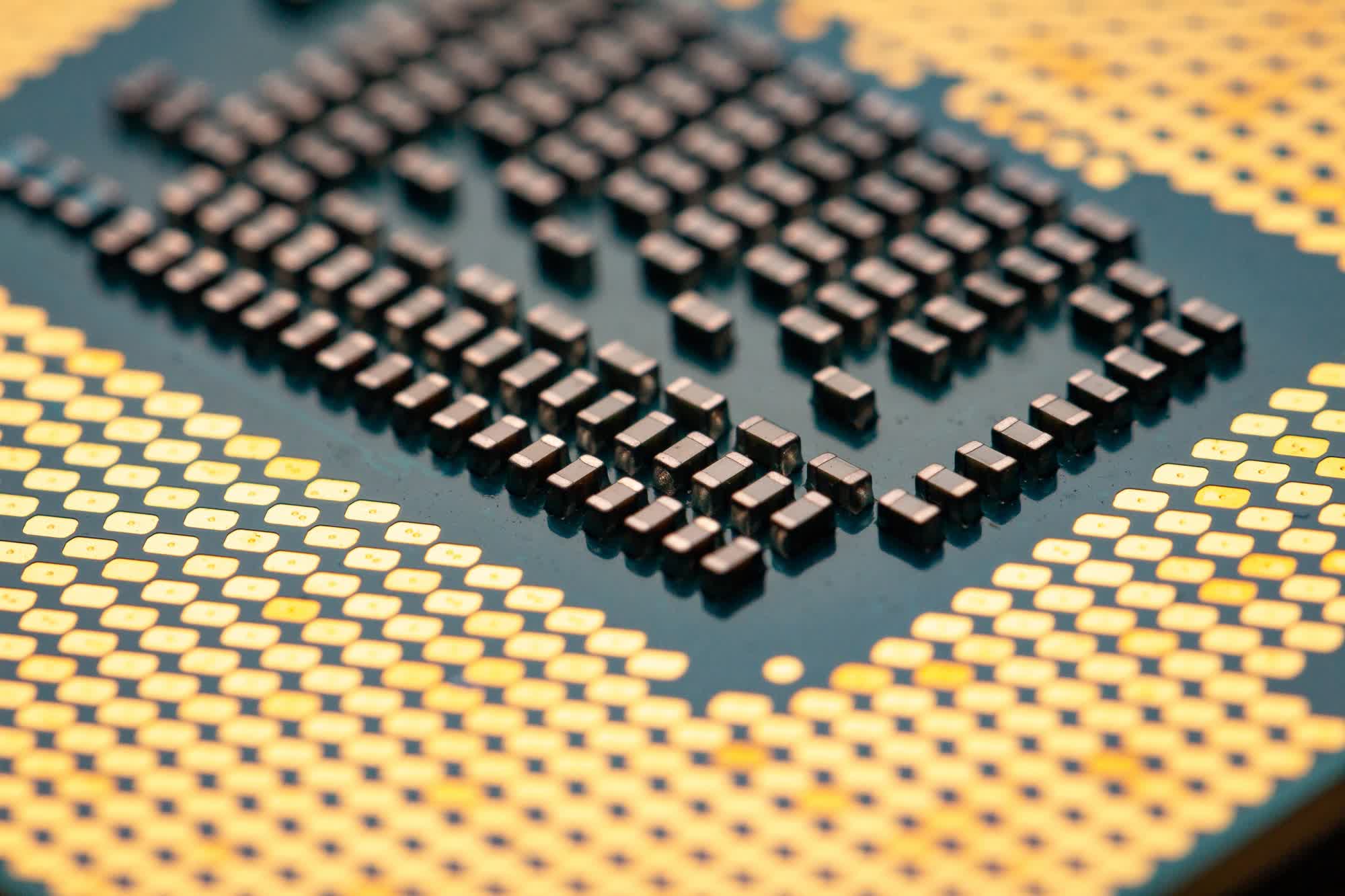
Image credit: Ryan, Brecht Corbeel