An unpatched exploit in Windows 7, Windows Server 2008 R2 and Windows 8 Consumer Preview allows a user to launch an elevated command prompt by manipulating the sticky keys function. The hack requires very little knowledge and can be exploited in a matter of seconds.
Neowin says that this exploit has been documented for some time but most tech users are unaware of it and how easy it is to accomplish. To install, a user simply needs to first gain access to an elevated command prompt and type the following code:
REG ADD "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sethc.exe" /v Debugger /t REG_SZ /d "C:\windows\system32\cmd.exe"
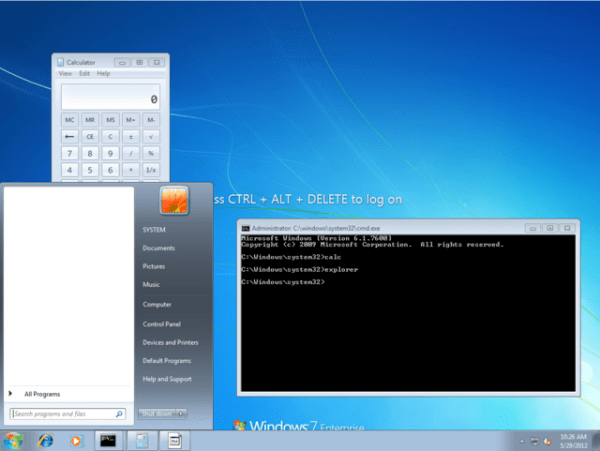
Depending on how fast you can type, this could easily be done in less than a minute. Once entered, a user can return to the workstation at a later date and launch the same high level command prompt at the login screen by pressing the Shift key five times. This usually activates sticky keys but the above code changes its function to launch the command prompt instead.
The publication points out that the hack is virtually undetectable aside from the registry key and even works via remote desktop session.
As you can imagine, this is a critical security hole should anyone get their hands on a workstation for a matter of seconds that isn't authorized to use the system. One possible scenario could involve a disgruntled employee activating the hack on multiple systems then returning after they have been terminated to steal or delete valuable data.
Microsoft has yet to comment on the exploit.