July 9 is the day thousands of PCs (and Macs) infected with DNSChanger will lose their ability to surf the web. Although the virus was introduced in 2007, according to the DCWG's data, as many as 500,000 computers may still be infected. This is a friendly reminder to make certain your computers are malware-free and that their DNS settings are nominal.
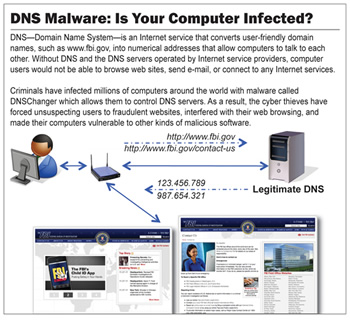
In 2011, the FBI busted the unscrupulous band of individuals responsible for DNSChanger, shutting down their Eastern European servers – a move which actually knocked millions of infected users off the web. Although those servers run by the criminals were used to feed infected users profitable ads, phishing attempts and malware, they also provided victims with a working DNS service – servers which allow human-friendly hostnames (techspot.com) to point to Internet locations that computers understand (IP address numbers).
Victims were left with computers configured to use DNS servers which no longer existed. As a result, nearly 4 million people were left without Internet access.
As a courtesy, FBI technorati organized an effort to temporarily provide DNS service for DNSChanger victims. After a period of time though, the FBI handed off this responsibility to the Internet Systems Consortium, a non-profit organization who has managed to keep the DNS flowing to infected users. However, this act of kindness will end on Monday.
How do I find out if I'm infected with DNSChanger?
Google and Facebook have been warning infected users. You can also manually check using this tool.
What should I do if I'm infected?
Visit DCWG for instructions and a list of utilities capable of removing DNSChanger from your computer. If none of these tools seem to work, your router's settings may have been changed by the virus (it does do that, believe it or not). You'll need to enter your router's web configuration (instructions vary) and change its DNS settings.
Virus scanners have been able to detect and prevent DNSChanger infections for some time now. Protect yourself!
Free anti-virus programs:
- Microsoft Security Essentials (no nagging!)
- Avast! (free version requires periodic re-registration)
- Avira (free version shows pop-ups on launch)\
- AVG (free version requires infrequent re-registration).