The US Department of Homeland Security is investigating claims that a researcher has found a SSL vulnerability in Siemens' RuggedCom network equipment. The security hole could reportedly be exploited by hackers to compromise the networks of critical infrastructure such as power plants.
"Justin W. Clarke publicly reported that the RSA Private PKI key for SSL communication between a client/user and a RuggedCom switch can be identified in the ROS. An attacker may use the key to create malicious communication to a RuggedCom network device," the report (PDF) by the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) for DHS noted.
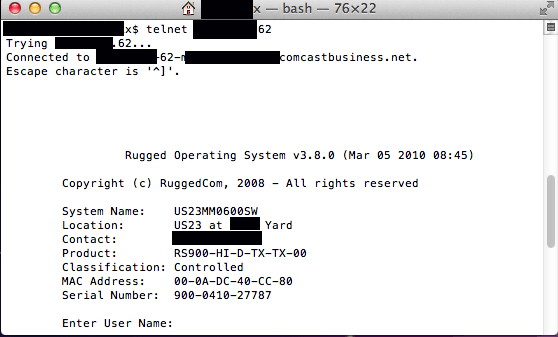
The security researcher disclosed the flaw when addressing delegates at a recent conference in Los Angeles, saying that Siemens used a single SSL key to decode all traffic encrypted across its network. "If you can get to the inside, there is almost no authentication, there are almost no checks and balances to stop you," Clarke said. Once a hacker has identified the private key it's possible to eavesdrop on all communications.
While the flaw doesn't appear to have been used in the wild, it would enable a hacker to remotely administer industrial control systems (ICS) as well as supervisory control and data acquisition systems (SCADA), which manipulate machinery in industrial settings. These include functions such as flipping switches or operating pumps and valves.
What is even more alarming is RuggedCom's routers are deployed extensively worldwide for mission-critical networks using ICS and SCADA equipment. They are used by electric sub-stations, railroad switches, the US Navy, Chevron and other authorities such as the Department of Transportation, opening up countless avenues of attack for hackers wishing to target such services.
The DHS says it's in contact with the hardware vendor and the researcher in order to patch the flaw as quickly as possible. Neither Siemens nor the DHS responded to requests for further information.
Image credit: Ars Technica