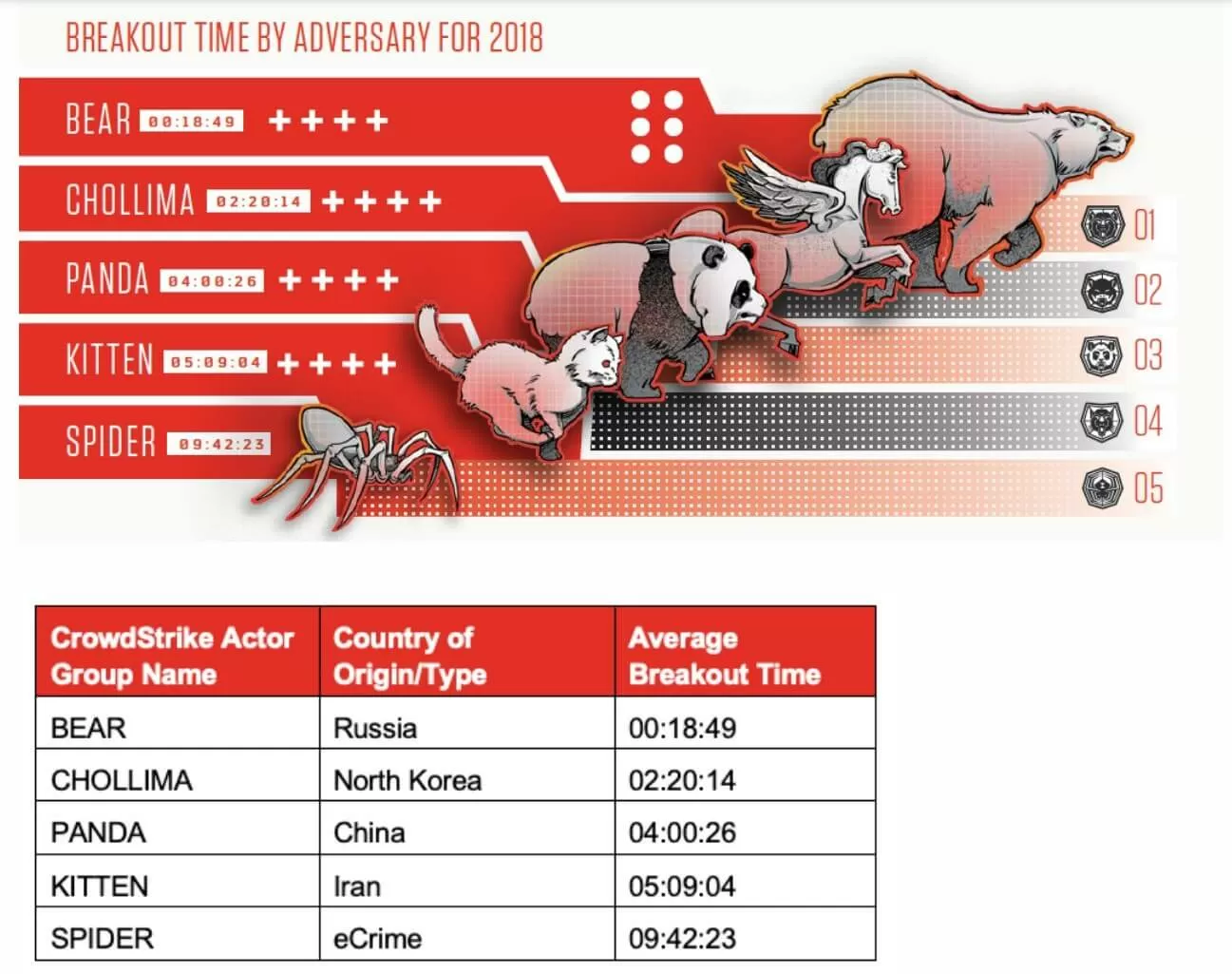
In brief: When it comes to hacking, speed is one of the most essential elements---for both attackers and defenders. That's why governments and companies should be worried about Russian nation-state actors, who take less than 20 minutes to start moving laterally through an organization's network after the initial breach. That's around eight times quicker than North Korean hackers
Cybersecurity firm CrowdStrike has released its latest Global Threat report, in which groups are ranked by their 'breakout time.' This refers to the time it takes for intruders to move through systems in a network after first gaining access. It's during this period that hackers can deploy exploits and steal information.
CrowdStrike based its data on 30,000 intrusion attempts, ranking the breakout times of groups believed to be working for Russia (Bear), China (Panda), North Korea (Chollima), and Iran (Kitten), as well as cybercriminal gangs (Spider).
Russia came top of the rankings with a time of 18 minutes and 49 seconds, much faster than second-place North Korea, which took 2 hours and 20 minutes. Chinese hackers were third with a breakout time of just over four hours, followed by Iran's 5 hours and 9 minutes. At the bottom of the group is the cybercriminals, who take just over 9 hours and 42 seconds.
"State-sponsored adversaries out of Russia (BEARS) ranked first --- almost eight times faster, on average, than their nearest competitor. While we certainly expected them to come out on top, given how effective their tradecraft usually is in comparison with other threat actors, even we were surprised by the data and how fast they can move inside a network once they get a foothold," said Dmitri Alperovitch, CrowdStrike co-founder and CTO.
The report also suggested that China has given up on a cybersecurity truce it made with the Obama administration back in 2015. The country targeted telecoms systems in Asia and the US last year and has been accused of stealing intellectual property from American companies. CrowdStrike believes we will see an uptick in these activities from Chinese-based hackers as the trade war with the US continues.
Image credit: BeeBright via Shutterstock