A hot potato: Intel revealed today in a security advisory that new vulnerabilities have been found inside its CPUs. This new batch of CPU flaws are yet another speculative execution type of exploit dubbed Fallout, RIDL and ZombieLoad. As had been discussed, in a post-Spectre IT world, more and more of these hard flaws will appear and as evidence suggests, there is no slowing them down.
We've come to learn more about speculative execution since the first Meltdown and Spectre flaws came to light, the performance-enhancing feature found in modern CPU architectures allow a CPU to process data before it's actually requested by a program or user. The benefit is that the CPU can concurrently process more data instead of sitting idle if resources are available. By trying to predict an outcome, CPUs can execute certain tasks ahead of time, making the system perform significantly faster.
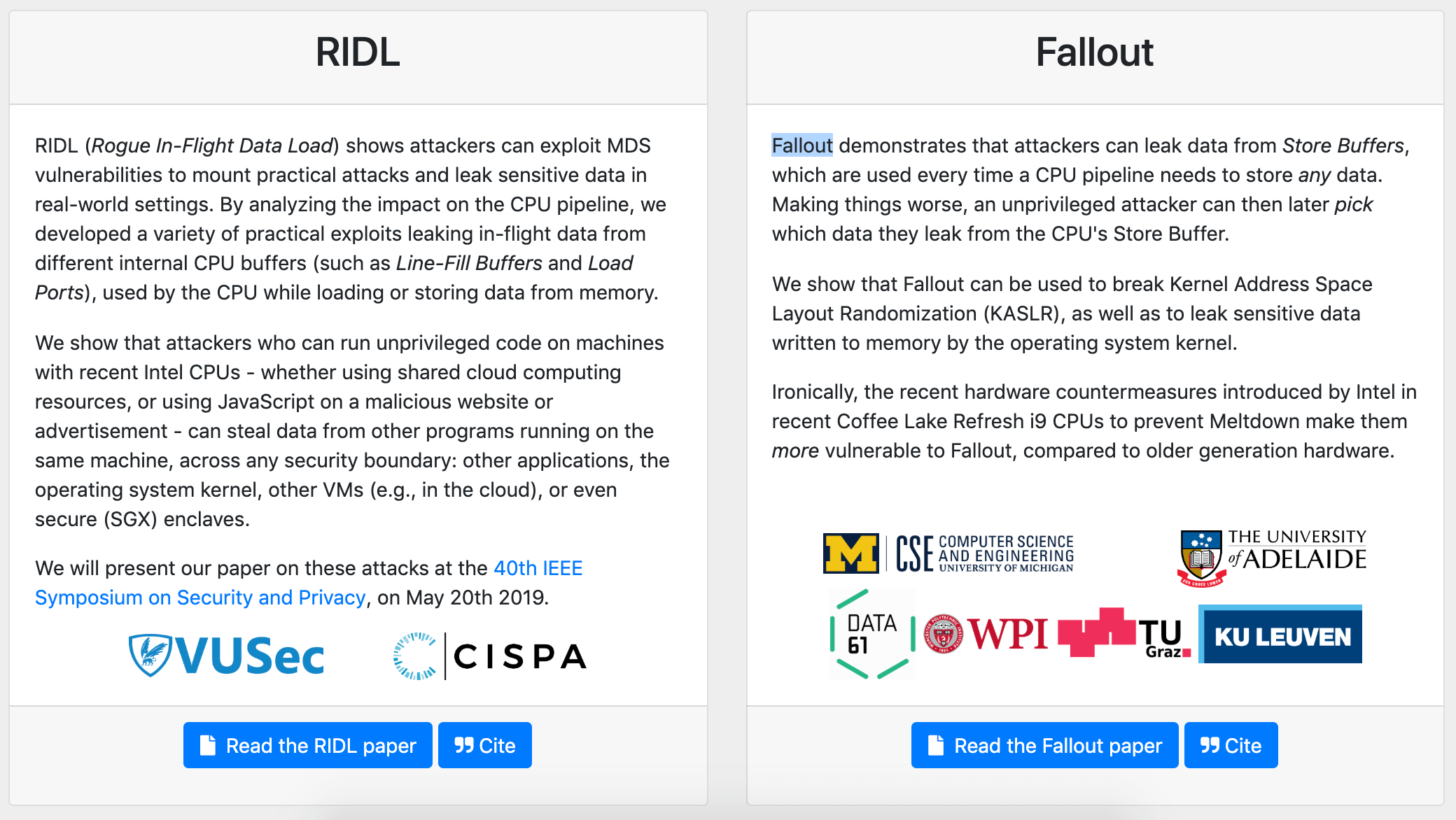
What nobody anticipated however is that speculative execution would open the door to many hard vulnerabilities that cannot be fixed outright but can be mitigated. According to RIDL (Rogue In-Flight Data Load) and Fallout's informational website (also see, ZombieLoad), these new flaws allow attackers to leak confidential data by exploiting Microarchitectural Data Sampling (MDS) side-channel vulnerabilities in Intel CPUs. Unlike previous Meltdown, Spectre and Foreshadow CPU flaws, the leaks do not occur at the CPU cache level but target arbitrary in-flight data from CPU internal buffers. Qualcomm and AMD processors are not affected by these flaws.
In terms of practical use, security researchers say an attack could be launched using malicious JavaScript in a web page or from a co-located Virtual Machine in the cloud, allowing them to leak confidential data present on your system such as passwords or crypto keys. These would require a certain level of local (not privileged) access in the first place, but that alone is no excuse to take the flaws lightly.
Intel is understandably more reserved about reporting the severity of the flaws. In this instance it would appear they already had identified the flaws internally and Intel's security researchers were working actively in mitigations. "Practical exploitation of MDS is a very complex undertaking. MDS does not, by itself, provide an attacker with a way to choose the data that is leaked."
According to Intel, MDS flaws have been addressed in hardware on select 8th and 9th-gen Core processors and 2nd-gen Intel Xeons. Older hardware (7th-gen Core and below) will receive processor microcode updates (which we know take its sweet time to make it to the end user), in addition to updates at the operating system and hypervisor software level.
Regarding the potential performance impact, Intel claims "when these mitigations are enabled, minimal performance impacts are expected for the majority of PC client application based benchmarks. Performance or resource utilization on some data center workloads may be affected and may vary accordingly." Looking at Intel's internal benchmark data does show that datacenter and storage sensitive workloads have the most potential to be affected.
There is some conflicting information regarding Hyper-Threading, with some researchers suggesting it should be disabled entirely on older generation Core CPUs. Google's Chrome OS 74 disables Hyper-Threading by default and is expected to deliver additional mitigations in the next version. Intel is not as resolute about the matter, indicating they do not recommend HT to be disabled, but users who "cannot guarantee that trusted software is running on their systems" may consider disabling it. Then again, who can fully guarantee your web browser and every website you visit is completely secure.
Another bit of conflicting information is about the affected processors, with Intel claiming 9th-gen Core CPUs are on the clear, while the group of Fallout's flaw researchers claim recent "hardware countermeasures introduced by Intel in Coffee Lake Refresh i9 CPUs to prevent Meltdown make them more vulnerable to Fallout, compared to older generation hardware."
Major OEMs and software vendors have been aware of the vulnerabilities for a period of time and have issued or are in the process of issuing patches. Microsoft has released software updates to help mitigate these vulnerabilities although the entire universe of PC hardware is not yet covered, upon availability of relevant microcode updates. Amazon's AWS cloud service has already been patched. Apple has released a security patch for macOS Mojave fixing most but not all Mac and MacBooks affected. Google has confirmed that nearly no Android devices are affected (mostly based on ARM SoCs), but Chromebooks have already been patched with mitigations.
As with previous CPU flaws, installing both operating system, software and firmware/microcode updates are necessary to become fully patched.