Phantasm66
Posts: 4,909 +8
OK, don't know if any of you use this, but I run an FTP server on my home machine, basically just using the in-built software which is included with Windows 2000, XP, etc... both on workstation and server versions.
Anyway, I use this to upload and download files to and from work. I have also made virtual directories for certain friends so that they can download files I make available for them such as up-to-date TV episodes I get from IRC, and so forth.
But there is a problem: My username and password are sent in unencrypted ASCII when I authenticate, and anyone in the path between my machine and the machine I am connecting from (i.e. anyone of the hosts you see listed when you do a traceroute) can see this information if they use some kind of network packet analyser software like Network monitor.
This is potentially bad news but not so bad, since there's probably only certain fairly safe stuff between myself (NTL user) and the client machines (mostly in the university where I work) but I still don't like the idea of it.
And there is another problem: ANYONE ELSE out there on the Internet can connect, or at least try to, leaving my FTP server open to some form of BRUTE FORCE attack from outsiders.... OBVIOUSLY I HAVE DISABLED ANONYMOUS CONNECTIONS but that doesn't stop some machines out there trying to connect anyway or try to guess what accounts DO have access....
NOW, I could use some more encrypted and safe means of connection, such as open SSH ( www.openssh.com ) but let's assume for the moment that I want to stick with FTP....
Well, what I discovered that you could do is grant or deny connections based on IP address, and that this could also apply to a range of addresses as well. Here is where its hiding:
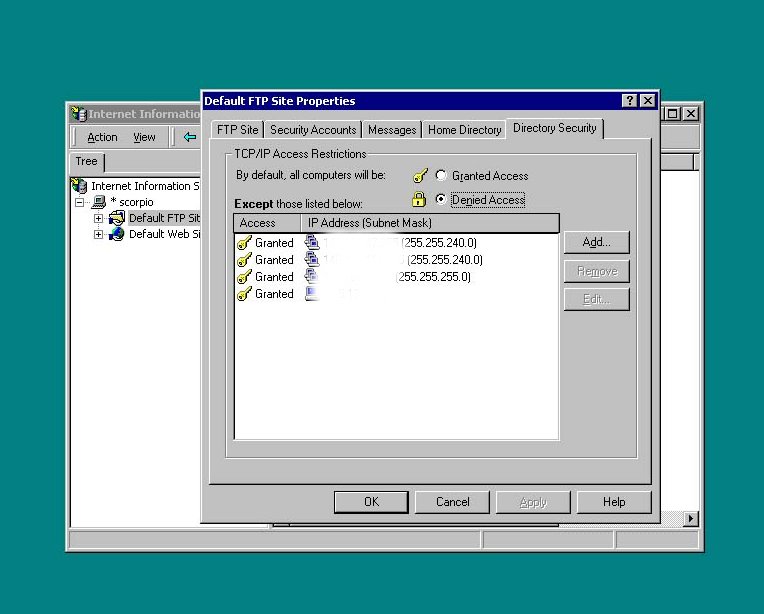
I had to firstly add my own IP address as a single host, and then added ranges of addresses because I wanted to be able to connect from any machine on certain networks at work. So for those, instead of entering the IP address of the host, I entered the broadcast address and subnet mask of the network. This is pretty simple to work out if you know a little about subnetting and can do a few binary calculations.
I've airbrushed this information away as I'm not too keen to broadcast this information, but its simple to get from your work or at home by looking at your tcp/ip settings with the ipconfig /all command in a command prompt.
I would add that I had to restart the FTP publishing service for this to take effect....
And, obviously, if you want a friend to be able to connect to your FTP server you will have to get their IP address and add it to the list of allowed connections.
Now there's no more hacker war ftp accesses from machines all over the net trying to hack into me to upload warez onto my machine or something.....
Good luck trying it, post back if you have any questions.
Anyway, I use this to upload and download files to and from work. I have also made virtual directories for certain friends so that they can download files I make available for them such as up-to-date TV episodes I get from IRC, and so forth.
But there is a problem: My username and password are sent in unencrypted ASCII when I authenticate, and anyone in the path between my machine and the machine I am connecting from (i.e. anyone of the hosts you see listed when you do a traceroute) can see this information if they use some kind of network packet analyser software like Network monitor.
This is potentially bad news but not so bad, since there's probably only certain fairly safe stuff between myself (NTL user) and the client machines (mostly in the university where I work) but I still don't like the idea of it.
And there is another problem: ANYONE ELSE out there on the Internet can connect, or at least try to, leaving my FTP server open to some form of BRUTE FORCE attack from outsiders.... OBVIOUSLY I HAVE DISABLED ANONYMOUS CONNECTIONS but that doesn't stop some machines out there trying to connect anyway or try to guess what accounts DO have access....
NOW, I could use some more encrypted and safe means of connection, such as open SSH ( www.openssh.com ) but let's assume for the moment that I want to stick with FTP....
Well, what I discovered that you could do is grant or deny connections based on IP address, and that this could also apply to a range of addresses as well. Here is where its hiding:
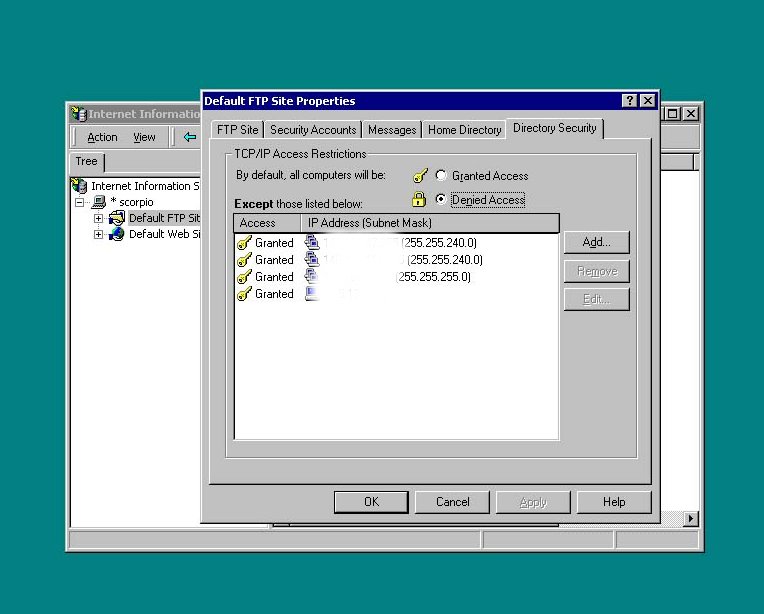
I had to firstly add my own IP address as a single host, and then added ranges of addresses because I wanted to be able to connect from any machine on certain networks at work. So for those, instead of entering the IP address of the host, I entered the broadcast address and subnet mask of the network. This is pretty simple to work out if you know a little about subnetting and can do a few binary calculations.
I've airbrushed this information away as I'm not too keen to broadcast this information, but its simple to get from your work or at home by looking at your tcp/ip settings with the ipconfig /all command in a command prompt.
I would add that I had to restart the FTP publishing service for this to take effect....
And, obviously, if you want a friend to be able to connect to your FTP server you will have to get their IP address and add it to the list of allowed connections.
Now there's no more hacker war ftp accesses from machines all over the net trying to hack into me to upload warez onto my machine or something.....
Good luck trying it, post back if you have any questions.