Why it matters: Microsoft has announced that it has successfully disrupted Trickbot’s botnet after it had ensnared some of its Office 365 users. The company submitted a legal request to take down the botnet infrastructure ran by hackers.

According to Microsoft, its Defender Antivirus team has been working alongside major cybercrime partners to collect samples and unravel critical information related to the botnet scheme. Participants in the cybersecurity data exchange group include FS-ISAC, Lumen’s Black Lotus Labs, ESET, Symantec, and NTT.
According to filed court documents, Microsoft sought permission to take over domains and servers belonging to the malicious Russia-based group. It also wanted legal assent to block IP addresses associated with the plot and prevent the entities behind it from purchasing or leasing servers.
The requests were part of a grander plan of action to destroy data stored in the hackers' systems. The intention was first to block access to servers controlling over 1 million infected machines. This move would be a crucial step in halting control of over an additional 250 million breached email addresses.
Microsoft has said that Trickbot’s strategy was mostly successful because it used a custom third-party Office 365 app. Tricking users into installing it allowed perpetrators to bypass passwords instead of relying on the OAuth2 token. Through this technique, they could access compromised Microsoft 365 user accounts and sensitive data associated with them, such as email content and contact lists.
In the court documents, Microsoft laments that Trickbot used authentic-looking Microsoft email addresses and other company information to malign its clients. It argues that the network used its name and infrastructure for malicious purposes, thereby tarnishing its image.
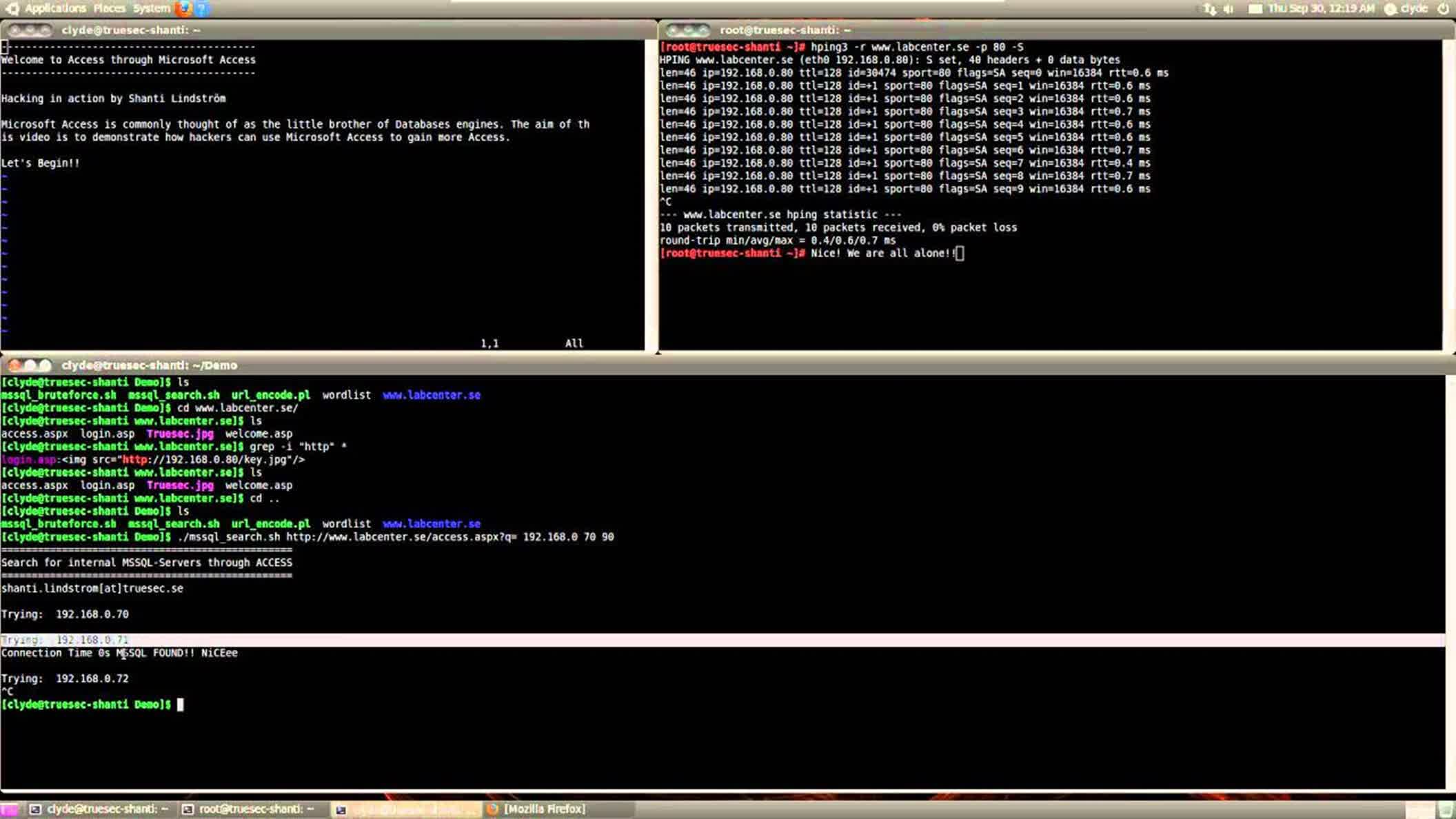
Tricking users into installing it gave perpetrators the opportunity to bypass passwords and instead rely on the OAuth2 token (credit: YouTube).
Researchers first detected the Trickbot network in 2016. It began as a banking Trojan and developed later into a multiplex malware installer. The updated worm went on to compromise millions of devices worldwide. The entities behind the network have, over the years, leased access to infected systems to other cybercrime syndicates. Analysts widely refer to this as Malware-as-a-Service (MaaS).
Despite Microsoft's and US government agencies' best efforts to take down Trickbot, security experts at Intel471 warn that the recent move appears to have had minimal impact. According to the company, the botnet network is extensively decentralized and utilizes IP masking networks such as Tor to obscure server locations. This elaborate approach minimizes damage caused by targeted takedowns.
As noted in the company’s latest report, “Microsoft’s list of Trickbot IP addresses contained four IP addresses at the time of this report and were being pushed by Trickbot’s operators as Trickbot command and control servers. At the time of this report, Intel 471 has not seen any significant impact on Trickbot’s infrastructure and ability to communicate with Trickbot-infected systems."
https://www.techspot.com/news/87082-microsoft-fights-botnet-after-office-365-malware-attack.html
