Be cautious out there! On Tuesday, security research firm RiskIQ exposed yet another MageCart group. This one is using phishing combined with card skimming to bilk consumers' bank accounts. The hackers seem pretty sophisticated when it comes to phishing, but less experienced at skimming.

The MageCart group is known as Fullz House and has been highly successful at maximizing its profits combining phishing with card skimming. RiskIQ analyst Yonathan Klijnsma told TechSpot that after carefully analyzing the group's tactics, he had two main takeaways.
[Fullz House is an] organized group running the sales as well as the theft of payment data and PII (personally identifiable information) from phishing pages for payment processors. Their skimming operation comes in two parts:
- Your every-day skimmer we've seen hundreds of times (they did build their own, which is a bit backward and looks more like the first skimming attempts we saw in 2014).
- A man-in-the-middle payment phishing page where a user normally is redirected to their bank to pay, they now get this phishing page, and once they enter their data are redirected to their real bank. The actual flow of the process is not interrupted, and they can finish their checkout process.
Fullz House appears to have been involved with its phishing operation for quite a while but has begun to use skimming techniques more recently. RiskIQ says it is not uncommon to see groups that are known to operate in one "ecosystem" to try something different. MageCart Group 4 specialized in banking malware, but last year began using card skimming attacks.
"Ultimately, the picture that emerges is of a well-connected group that has access to bulletproof hosting, is schooled in the world of phishing, and, although new to web-skimming, has the cunning to make a niche for themselves."
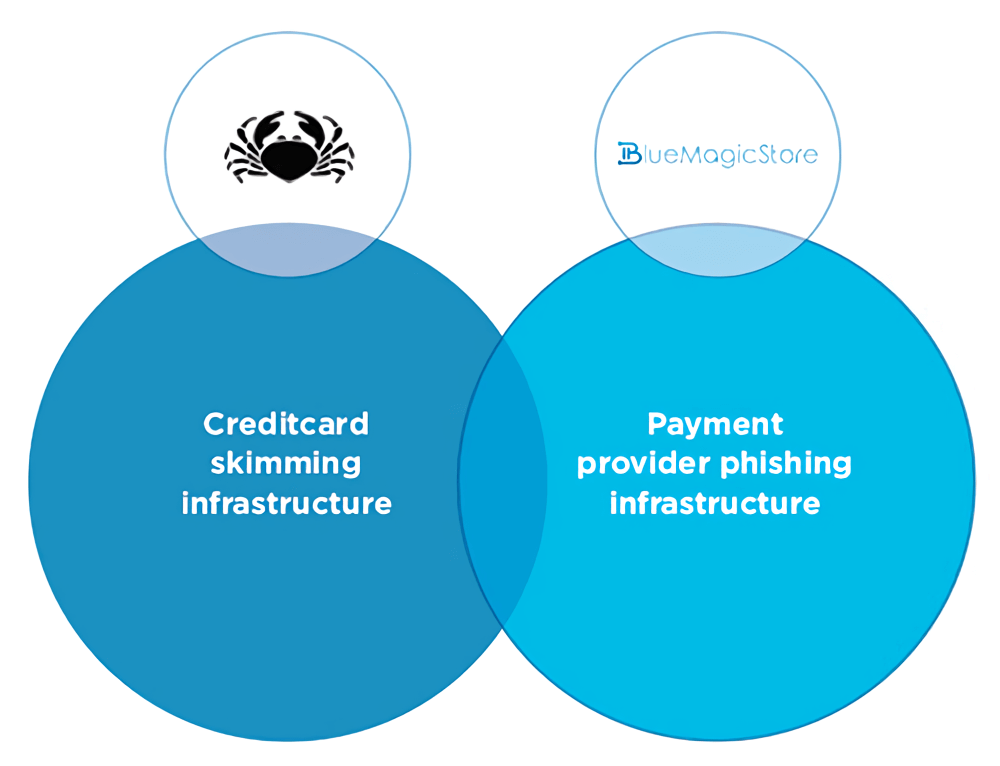
The group has been in operation for some time and has two "stores" where it sells its information. The "BlueMagicStore" sells full packages of PII and financial information, while another marketplace called "CardHouse" traffics in stolen credit card numbers and security codes. While the two vending sites have been around for at least a year, RiskIQ says that activity of Fullz House and its new methods escalated beginning in August-September of 2019.
The group's phishing technique is very efficient. They have templates of payment provider pages that they reconstructed (not copied) from the real deal, with a single backend handling them all. While they are known to target multiple sites, PayPal seems to be Fullz House's go-to domain.
The card skimming aspect of the operation is similar to others. However, RiskIQ found it particularly interesting that it uses code that the group seems to have built itself. The researchers say this is unusual because most skimming outfits use pre-made skimmer kits. There are very few operators that maintain their own code.
The other thing that sets the Fullz House skimmer apart from the rest is that it does not wait for the transaction to complete before stealing the information. It scans every data field for changes and then relays it to a "drop location" where it is packaged and disguised as an image file.
According to RiskIQ, this is a very crude method that was actually used in 2014 by the very first skimming group.
"This implementation is primitive and works more like a keylogger with data validation than a skimmer," said Klijnsma in his report. "As we mentioned, these criminals are new at skimming and [are] figuring it out as they go."
Just because Fullz House is inexperienced at skimming, it has still shown innovation in the ecosystem. RiskIQ notes the group has repurposed its skimmers, to implement an ingenious man-in-the-middle attack on transactions.
After visitors select what they want to buy on a compromised website and click the link to the payment page, they are redirected to a fake transaction screen controlled by Fullz House. After entering their payment information and hitting "Pay," the client is sent back to the real payment processing screen of the website where the purchase is completed. Neither the compromised website nor the customer is aware that anything nefarious happened during the transaction.
Klijnsma has published all the technical details, including code snippets, on the RiskIQ website for those interested in all the gory details.
mage credit: RiskIQ