Wireshark is the world's leading network protocol analyzer, trusted by professionals across enterprises, governments, non-profits, and academia. It provides deep visibility into network activity, allowing users to inspect traffic at a granular level – essential for troubleshooting, analysis, development, and education.
Originally created by Gerald Combs in 1998, Wireshark has grown into a thriving open-source project powered by a global community of expert contributors and volunteers.
What should I look for when analyzing packets in Wireshark?
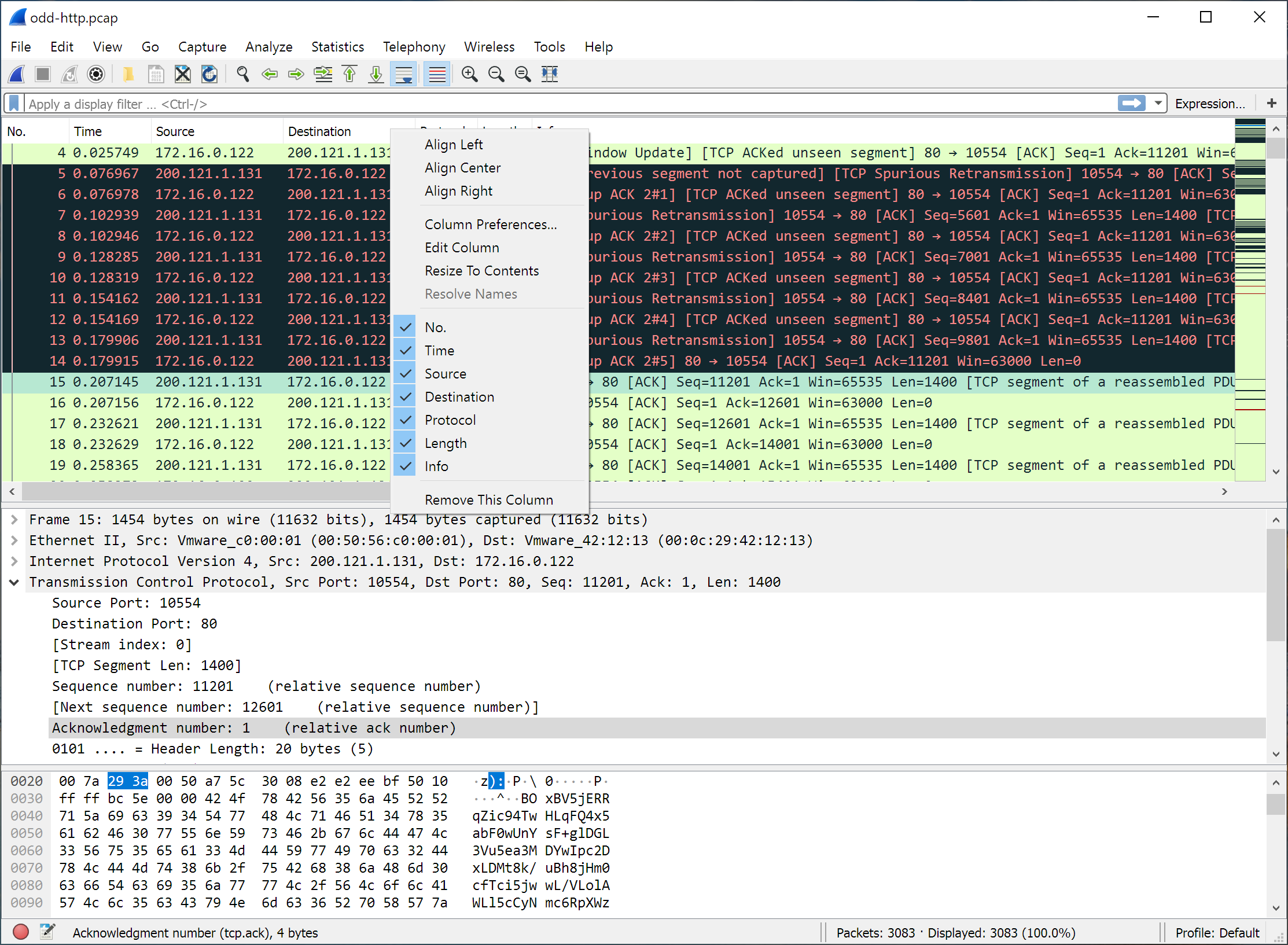
Wireshark is a powerful tool for troubleshooting specific network issues. Instead of scanning all traffic, focus on a particular problem, such as slow application performance or failed connections. Use filters to narrow down the data and look for anomalies like retransmissions, handshake failures, or unexpected protocol behaviors.
By applying filters based on IP addresses, protocols, or specific packet attributes, you can focus on the most relevant data for your analysis.
How do I filter traffic to a specific website in Wireshark?
To filter traffic for a specific website, first determine its IP address using the command nslookup [website] (e.g., nslookup www.techspot.com). Then, apply the filter ip.addr == [IP_ADDRESS] in Wireshark to isolate packets related to that site. For analyzing TCP connections, you can use filters like tcp.flags.syn == 1 && tcp.flags.ack == 0 to identify SYN packets
How can I capture traffic from specific devices on my network?
Capturing traffic from specific devices may require configuring your network appropriately. Use port mirroring on a managed switch or employ a network tap to direct the desired traffic to your monitoring system. Additionally, focusing on specific protocols, such as DNS, can provide insights into device activities.
Is Wireshark suitable for professional use in network analysis?
Yes. Wireshark is widely used in professional environments for network troubleshooting and analysis.
Features
- Deep inspection of hundreds of protocols, with more being added all the time
- Live capture and offline analysis
- Standard three-pane packet browser
- Multi-platform: Runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others
- Captured network data can be browsed via a GUI, or via the TTY-mode TShark utility
- The most powerful display filters in the industry
- Rich VoIP analysis
- Read/write many different capture file formats: tcpdump (libpcap), Pcap NG, Catapult DCT2000, Cisco Secure IDS iplog, Microsoft Network Monitor, Network General Sniffer (compressed and uncompressed), Sniffer Pro, and NetXray, Network Instruments Observer, NetScreen snoop, Novell LANalyzer, RADCOM WAN/LAN Analyzer, Shomiti/Finisar Surveyor, Tektronix K12xx, Visual Networks Visual UpTime, WildPackets EtherPeek/TokenPeek/AiroPeek, and many others
- Capture files compressed with gzip can be decompressed on the fly
- Live data can be read from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others (depending on your platform)
- Decryption support for many protocols, including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Coloring rules can be applied to the packet list for quick, intuitive analysis
- Output can be exported to XML, PostScript®, CSV, or plain text
What's New
- On macOS a lower resolution Wireshark icon is displayed in the App Switcher and Launchpad. sbug20544.
- Encoding on NAS5GS- NASDL Transport Message-Multiple Container contains inconsistencies. wsbuglink:20679].
- Bad resolver in Delegated Credential (RFC 9345) of TLS 1.3 CertificateRequest message. wsbuglink:20728].
- Ciscodump fails to start capture on Cisco IOS. Issue 20655.
Bug Fixes
- wnpa-sec-2026-05 USB HID dissector memory exhaustion. Issue 20972. CVE-2026-3201.
- wnpa-sec-2026-06 NTS-KE dissector crash. Issue 21000. CVE-2026-3202.
- wnpa-sec-2026-07 RF4CE Profile dissector crash. Issue 21009. CVE-2026-3203.
- The following bugs have been fixed:
- Wireshark doesn't start if Npcap is configured with "Restrict Npcap driver's Access to Administrators only" Issue 20828.
- PQC signature algorithm not reported in signature_algorithms. Issue 20953.
- Unexpected JA4 ALPN values when space characters sent. Issue 20966.
- Expert Info seems to have quadratic performance (gets slower and slower) Issue 20970.
- IKEv2 EMERGENCY_CALL_NUMBERS Notify payload cannot be decoded. Issue 20974.
- TShark and editcap fails with segmentation fault when output format (-F) set to blf. Issue 20976.
- Fuzz job crash: fuzz-2026-02-01-12944805400.pcap [Zigbee Direct Tunneling Zigbee NWK PDUs NULL hash table] Issue 20977.
- Wiretap writes pcapng custom options with string values invalidly. Issue 20978.
- RDM status in Output Status (GoodOutputB) field incorrectly decoded in Art-Net PollReply dissector. Issue 20980.
- Wiretap writes invalid pcapng Darwin option blocks. Issue 20991.
- TDS dissector desynchronizes on RPC DATENTYPE (0x28) due to incorrect expectation of TYPE_VARLEN (MaxLen) Issue 21001.
- Only first HTTP POST is parsed inside SOCKS with "Decode As". Issue 21006.
- TShark: Bogus "Dissector bug" messages generated in pipelines where something after tshark exits before reading all its input. Issue 21011.
- New Diameter RAT-Types in TS 29.212 not decoded. Issue 21012.
- Malformed packet error on Trigger HE Basic frames. Issue 21032.