Mobile security firm, Lookout, warns of a new malware which may be spreading itself to unsuspecting Android handsets and tablets. Coined as "NotCompatible", the malware is being propagated via Android's web browser which is thought to be a first for the mobile OS.
Before mass panic sets in through, there are a couple of things Android users should know. First, the malware doesn't seem to do anything malicious – not yet. Secondly, NotCompatible still requires user intervention in order to install it.
Although viruses, trojans and other digital nasties commonly exploit browser vulnerabilities in the computer realm, there have been very few examples of this in the mobile universe. NotCompatible doesn't actually exploit Android's web browser; moreover, it takes advantage of some poor design decisions which can be used to trick less sophisticated users into installing it.
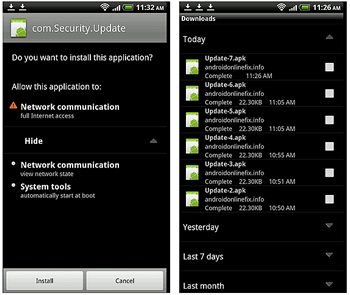
Here's how it works: The bug lives in a hidden iframe on infected websites. The malware then spreads itself by sending an infected .apk file to the user's phone or tablet guised as an automatic download (which Android's browser allows). As with any virus or malware, just downloading it isn't enough though – it needs to be executed. Once the file is finished downloading, the website alerts the user that a new system update is available. If an unsuspecting user falls for the notification, it will install the .apk file and give NotCompatible ongoing access to the device.
Infected websites commonly have the following code inserted into the bottom of each page:
We're still in the process of assessing the full extent of infected sites; however, there are early indications that the number of affected sites could be numerous.
Source: blog.mylookout.com
Although NotCompatible doesn't have any known payload or risk at the moment, it is possible that the malware could function as a trojan or proxy to something more malicious.
Two domains which currently house the malware, gaoanalitics.info and androidonlinefix.info, were singled out. According to Lookout though, there are many more. The firm also says the command and control domain seems to be notcompatibleapp.eu which happens to be the origin of its namesake.