Flame or Flamer, an admittedly sophisticated piece of malware, appears to have more tricks up its sleeve than security researchers had initially believed. Security firm Kaspersky has discovered that the virus turns infected PCs into Windows Update servers which may then fool uninfected PCs into downloading and installing Flame.
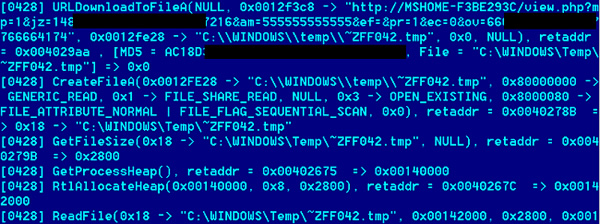
The multi-phase attack begins with an infected Windows PC laced with illegitimate security certificates – certs which appear to be digitally signed by Microsoft. Patient zero then advertises itself across the network as an proxy server, funneling Internet traffic through itself and cementing its man-in-the-middle role. Other Windows computers discover the infected computer and begin automatically using it as a proxy. When those unsuspecting PCs begin to download and install their regularly scheduled Windows Updates, the false proxy server substitutes requests for legitimate updates with its own versions – packaged installers for Flame.
To spread across a network, Flame relies on "automatically detect [proxy] settings" being active, an option found Control Panel > Internet Options > Connections. Unfortunately, this option is enabled automatically on most default Windows installs unless explicitly disabled by the user or through group policies.
Although clever and obviously dangerous, there's little need for panic just yet. Flame continues to be isolated in the Middle East and purposefully so, experts believe. The virus also further narrows its scope by targeting government networks, meaning everyday Internet citizens should be safe, at least for the moment.
It is unlikely that you are the target of Flamer unless you are an official in a Middle Eastern government or working on weapons research for such a government. Flamer is not "out there" on the Internet right now, spreading from country to country. You are not likely to find Flamer attached to an email in your Outlook Inbox (USB flash drives seem to be Flamer's infection vector of choice). And if you are using a good antivirus product it is now protecting you from Flamer. The major AV products were quickly updated to detect Flamer and the better ones will now have generic detection of malware that has "Flamer-like" characteristics.
Even though Flame may itself remain in isolation due to apparent political motivations, don't be surprised if other virus writers try to capitalize the ingenuity displayed by Flame's numerous modules.
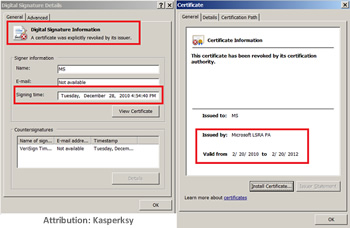
Fooling Windows Update on a PC is no trivial matter but Flame's designers managed to do something that no other malware creator has been known to do thus far – make a illegitimate certificate which Windows wholeheartedly believes is signed by Microsoft. This has long been the holy grail of malware writers, according to F-Secure and it brings with it some potentially scary consequences. This ability of Flame is key to its seamless subversion of Windows Update.