Mat Honan, a senior writer for Wired had his digital life turned upside-down on Friday after a cybercriminal gained access to his Amazon, Apple ID and Google accounts in a bid to target his three-letter long @mat Twitter account. The chain-reaction of events resulted in all three of his Apple devices being wiped as well as his Google account being terminated.
Honan reached out to his attacker, who calls himself "Phobia," offering the person immunity from prosecution in return for revealing how he did it. What unraveled is a lesson for everybody and exposes fundamental flaws in the security management at both Amazon and Apple.
Phobia used social engineering to reach his milestone; nothing was "hacked" using brute force. Phobia saw Honan's Twitter was linked to his personal website, which in return listed his email address for Gmail.
At this point he guessed the same email was used for Twitter, and went ahead and tried Google's account recovery page. Because two-step authentication was disabled, it revealed his backup email address was from an Apple .me account. Several characters were hidden, but enough was revealed to make it an easy guess, since Honan used the same characters for several of his email accounts with other providers.
"You honestly can get into any email associated with Apple," Phobia proclaimed, pointing out that either two-step verification on Gmail or using a provider other than Apple would have likely stopped him in his tracks.
Phobia then did a whois search on Honan's personal domain, which revealed his full postal address. The same information was available from Spokeo, WhitePages and PeopleSmart so getting a hold of it isn't as hard as you'd think. With this information in hand the attacker was able to take advantage of flaws in Amazon's security practices. He phoned Amazon pretending to be Honan and added a fake credit card to his account. Amazon only asks for the account name, billing address and an associated email address as proof.
He then called back and stated he had lost access to his account. After using the same pieces of information plus the last four digits of the fake credit card number, he was able to pass security, and add a new email address to the account. Phobia visited the Amazon website, entered the new email address and reset the password, then logged in and retrieved the last four digits of Honan's real credit card.
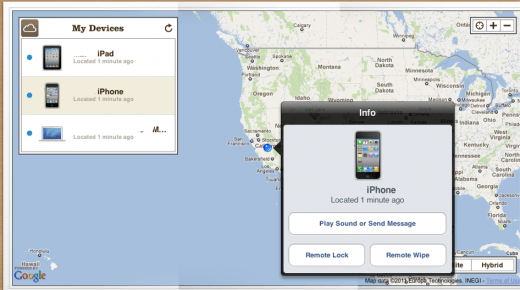
At this point Phobia was able to call AppleCare and use the last four digits of Honan's real credit card to 'verify' his identity. He was issued a temporary password to log into Honan's Apple ID account, resetting the password in the process. Once in, Phobia's partner wiped Honan's Macbook, iPhone and iPad just minutes apart, courtesy of Apple's iCloud "Find my" feature, which enables owners to remotely wipe devices if lost or stolen.
Honan had absolutely no idea any of this was going on until his iPhone suddenly stopped working. He was unable to enter the PIN to reverse the wipe process because the attacker created the PIN when scheduling it.
Phobia then reset Gmail's password via the compromised Apple email account, and from there the password on Twitter to gain access, announcing "Clan Vv3 and Phobia hacked this twitter." Honan's Google account was subsequently terminated by his attackers.
Ultimately, he was able to restore access to his Apple ID account, but a lack of backups resulted in him losing many irreplaceable files, such as his entire photo collection of his young daughter. Similarly, the termination of his Google account resulted in the loss of thousands of emails.
Amazon has since plugged the "social engineering" flaws and no longer allows customers to change account settings over the phone.
Interestingly, Apple for its part places the blame on its customer advisers. "Apple takes customer privacy seriously and requires multiple forms of verification before resetting an Apple ID password [...] we found that our own internal policies were not followed completely," they said in a statement. Apple has since reported that it has frozen over-the-phone password resets while it evaluates a better long-term solution.
There are several lessons everyone can learn from this. Firstly, additional security layers such as two-step authentication offered by Google and others drastically reduces the risk of social engineering attacks. Performing regular backups would have prevented Honan losing all his precious data, and using multiple email addresses with the same handle puts you at increased risk by making guessing additional accounts easier.
