Skype users beware: Kaspersky has discovered a new trojan that's spreading through Microsoft's chat service. Revealed late last week, the malware campaign is believed to have only began on March 1 but has grown rapidly and the infection is essentially being distributed through crafty spam.
Users are reportedly receiving unsolicited messages encouraging them to click a link. In one example, the spam read "i don't think i will ever sleep again after seeing this photo," while another asked the recipient to critique a picture the sender supposedly edited. Naturally, the links lead to malware.
Once you've clicked the bait and the infection takes root, the attackers can gain control of your machine and can use it to do their bidding – mining Bitcoins in this case. Bitcoins are created simply by using a system's CPU and GPU resources, which makes it an attractive revenue option for botnet operators. The decentralized digital currency is currently trading for more than $180 per unit and has gained popularity over the last year as an anonymous means of exchange, further adding to its appeal among cybercriminals.
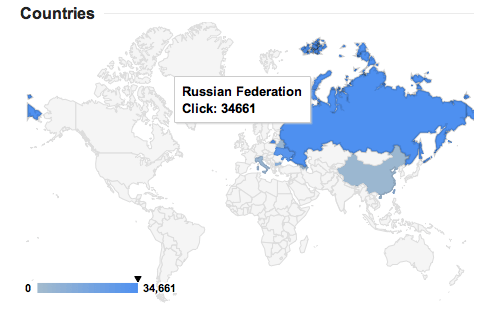
Kaspersky reports that most of the victims are located in Russia and Ukraine, though users across China, Italy, Poland, Taiwan, Bulgaria, Costa Rica, Spain, Germany and more are also affected. The trojan has been quite active as the malicious URL was gaining about 10,000 clicks per hour – or 2.7 per second if you prefer – as recent as last week. The initial infection is known to be downloaded from a server in India, but once your system is compromised it's loaded with additional malware from elsewhere too.
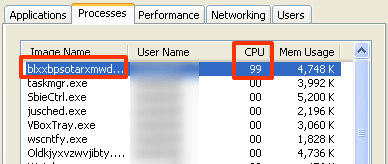
It doesn't seem like there's a quick and easy method to making sure you aren't infected, though it's safe to assume something isn't right if your CPU and/or GPU are running at unusually high loads – especially if a mysterious system process is using all your resources. The detection rate on VirusTotal is said to be pretty poor with only 12 of 46 antiviruses finding the infection. Of course, Kaspersky's security software is among the few that can detect the trojan and it's identified as "UDS:DangerousObject.Multi.Generic."
