A cybersecurity startup called Cryptonite (not to be confused with the cryptocurrency) just release a technology that obfuscates a network in such a way that hackers cannot get a view of its topology.
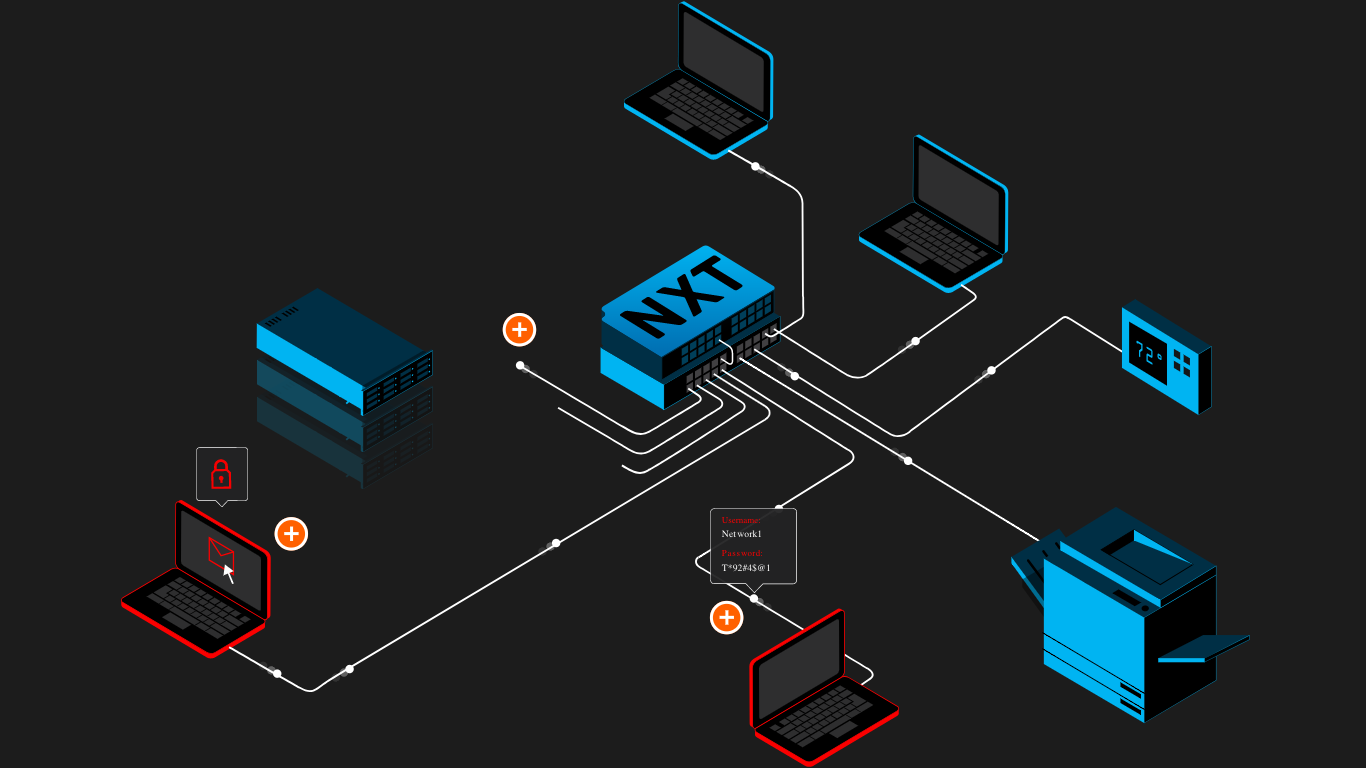
The device, called CryptoniteNXT, sits between the internal network and the perimeter firewall and blocks malicious activities. More importantly, it also obscures the network's layout. The company refers to it as a "Moving Target Cyber Defense" because it alters the way the network "looks" from any given entry or endpoint, essentially blinding attackers.
"Moving Target Cyber Defense places attackers in a shapeshifting environment where IP addresses can no longer be used to enumerate a network and plan an attack," says the firm's website. "Attacker tools no longer work at all, and lateral east-west movement is all but shut down. Cyber attackers cannot target what they cannot see, and cannot attack without a target."
CryptoniteNXT transforms a network of static IP addresses into a network full of dynamic addresses. What's more, the view from any endpoint or malicious device will be different from another. When trying to infiltrate from multiple locations, attackers will be presented with differing topologies. Additionally, any information gained is restricted to a limited time, making it difficult to perform malicious actions.
According to Cryptonite, the closest alternative to the defense it provides is Cisco's TrustSec. However, where the Cisco offering is a software-based segmentation technology, CryptoniteNXT is a hardware alternative that is architecturally independent, so it does not require upgrades or changing of existing network equipment.
According to The Register, the company's tech evolved from a project funded by the US Department of Defense and Homeland Security. From there, Cryptonite spun out from parent company Intelligent Automation (a Maryland defense contractor) with funding from various cybersecurity investors including Tenable founder Ron Gula.
Gula's investment was not solely limited to an interest in receiving an ROI. He actually deployed the tech within his organization, Gula Tech Adventures.
"I invested in Cryptonite because they uniquely prevent our adversaries from exfiltrating actionable information from our networks," he said. "The other key capability is their fine-grained micro-segmentation, which stops east-west traffic that has enabled the spread of ransomware."
Cryptonite is also partnering with Aruba ClearPass and Palo Alto Networks on joint ventures that are to be announced in weeks to come.