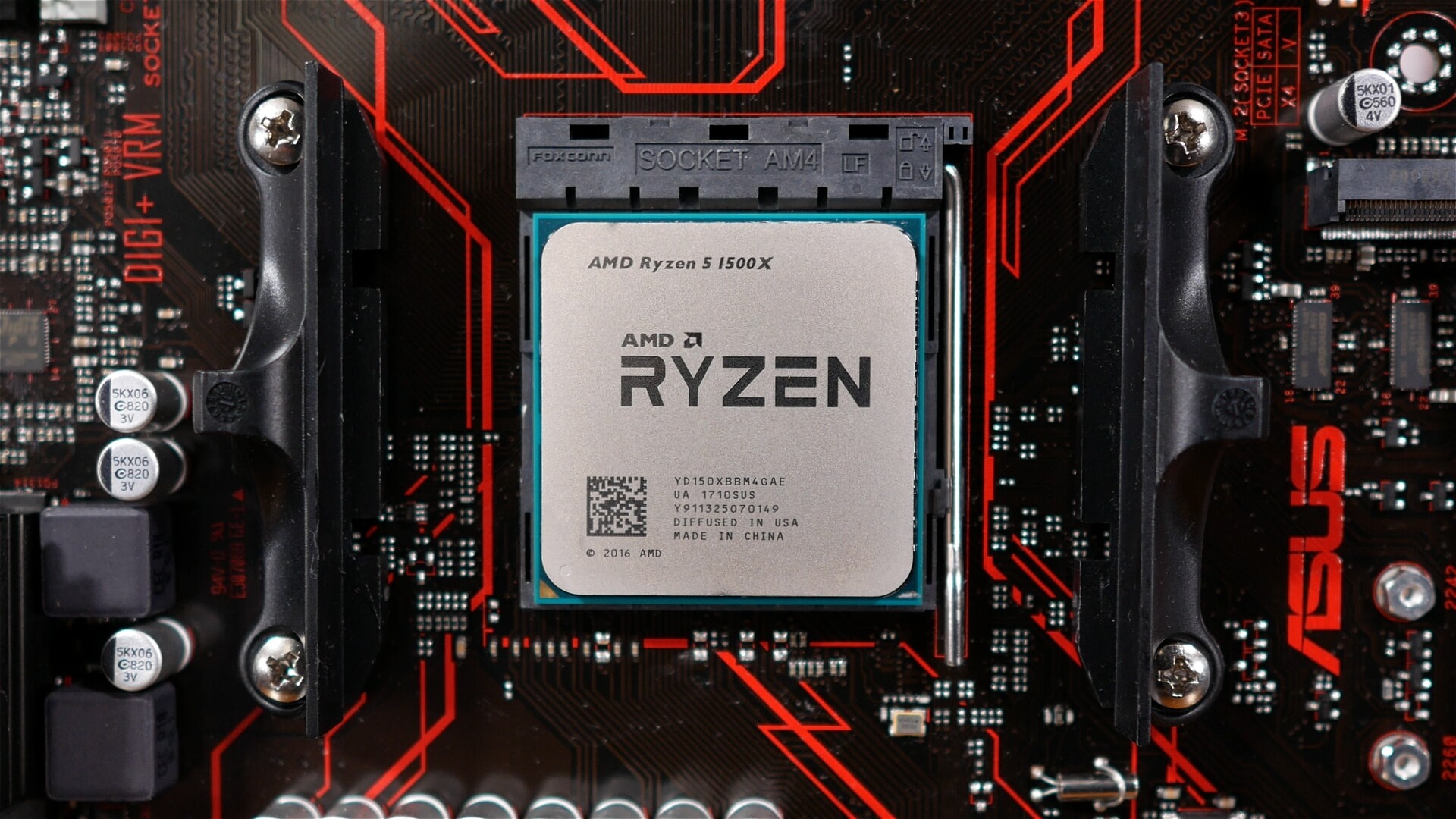
Israeli-based security company CTS-Labs on Tuesday said it has discovered 13 critical security vulnerabilities and exploitable manufacturer backdoors impacting AMD's latest Epyc, Ryzen, Ryzen Pro and Ryzen Mobile lines of processors.
CTS has classified the vulnerabilities, which it found over the course of a six-month investigation, into four categories they're calling Ryzenfall, Masterkey, Fallout and Chimera.
Full details on each vulnerability can be found in CTS' 20-page whitepaper (our brief summary can be read below, too). Fortunately, specific technical details that could be used to exploit the vulnerabilities have been omitted. It's also worth noting that AMD has been made aware of the issues, as have "select security companies" that could help mitigate the fallout and US regulators.
An AMD spokesperson told CNET it is investigating the report, which they "just received." According to the publication, CTS gave AMD less than 24 hours notice before going public with their findings. Standard practice in the industry is to give 90 days notice prior to publicly announcing a vulnerability. "At AMD, security is a top priority and we are continually working to ensure the safety of our users as new risks arise. We are investigating this report, which we just received, to understand the methodology and merit of the findings," that's AMD's statement we received via email today.
The flaws, which impact the AMD Secure Processor, can reportedly allow an attacker to take control over Ryzen and Epyc processors as well as Ryzen chipsets. CTS also says a bad actor could infect chips with malware, steal credentials on high-security enterprise networks and cause physical damage to hardware, all while remaining virtually undetectable by most security solutions.
Who is the source?
While we await for AMD's official response on the reported flaws – after all, they were barely given any notice – and we can't comment on the merit of the actual flaws since the technical details have been purposely omitted for security reasons, we can mention the obvious: this all looks a bit too well coordinated.
Intel's now infamous Meltdown and Spectre CPU flaws were discovered by Google's Project Zero team last year, and when the information leaked a tad early last January, Intel and many other parties involved had already months to prepare on how to inform the public and for the patching rollout. Whether they did a poor job or not, that's entirely a different conversation.
In this scenario, now hitting AMD CPUs exclusively (that we know so far), the source of the flaws is Israel-based CTS-Labs, a security firm formed in 2017. The company claims they've been investigating these AMD chip issues for six months, but their website went live in June 2017, so perhaps the sole purpose of this enterprise has been to look into AMD chip flaws that can stand next to Meltdown and Spectre. And who is to benefit from this? Surely the public and AMD customers, but there is another obvious answer to that question.
The informational website, AMDflaws.com, maintained by CTS-Labs, notes "this site is to inform the public about the vulnerabilities and call upon AMD and the security community to fix the vulnerable products," however in the legal footnotes of the aforementioned whitepaper you will find a more telling remark: "Although we have a good faith belief in our analysis and believe it to be objective and unbiased, you are advised that we may have, either directly or indirectly, an economic interest in the performance of the securities of the companies whose products are the subject of our reports."
A brief summary of the four flaws as discovered by CTS-Labs follows below.
Masterkey
Masterkey is a set of three vulnerabilities that collectively allow malicious actors to install malware inside the secure processor. From here, the researchers say malware could bypass secure boot and inject code directly into a computer's BIOS or operating system and disable firmware-based security features within the secure processor like Secure Encrypted Virtualization (SEV) or Firmware Trusted Platform Module (fTPM).
Because most Epyc and Ryzen motherboards on the market use a BIOS from American Megatrends that allows reflashing from within the OS using a command-line utility, CTS says Masterkey can often be exploited remotely.

Ryzenfall
CTS describes the four Ryzenfall vulnerabilities as a set of design and implementation flaws within AMD Secure OS, the operating system in charge of the secure processor on Ryzen, Ryzen Pro and Ryzen Mobile chips. At their worse, Ryzenfall can be exploited by malware to allow for the secure processor to be completely taken over.
Ryzenfall can also be exploited to allow access to protected memory regions that are otherwise sealed off by hardware including Windows Isolated User Mode and Isolated Kernel Mode (VTL1), Secure Management RAM (SMRAM) and AMD Secure Processor Fenced DRAM. Breaking this "hardware security seal" could have multiple security implications, CTS says.
Fallout
The Fallout class is a set of three design-flaw vulnerabilities that CTS says are found inside the boot loader of Epyc's secure processor. Like Ryzenfall, they can be exploited to allow access to Windows Isolated User Mode and Isolated Kernel Mode (VTL1) and Secure Management RAM (SMRAM), areas that should be completely inaccessible to user programs and kernel drivers running inside the operating system.
CTS says malicious hackers could exploit Fallout vulnerabilities to disable protections against unauthorized BIOS reflashing within system management mode, inject malware into VTL1 and bypass Microsoft Virtualization-based security, the latter of which could be used to steal network credentials - behavior CTS says is often a precursor to lateral network movement as part of a remote attack.
Chimera
Chimera is a class of vulnerabilities that encompass an "array of hidden manufacturer backdoors" within AMD's Promontory chipsets, a key part of all Ryzen and Ryzen Pro workstations.
Specifically, there are two sets of backdoors - one that is implemented within firmware running on the chip and another inside the chip's ASIC hardware. Since the latter has been manufactured into the chip, CTS concedes that it may not be possible to fix it, adding that AMD may have to resort to a recall or some other sort of workaround.
A system's chipset is connected to all sorts of functionality and features, from USB, SATA and PCIe ports to a computer's Wi-Fi, LAN and Bluetooth systems. As such, running malware here could have numerous consequences on a system's security.
In testing, CTS claims it has been able to execute its own code within the chipset and leverage the Direct Memory Access (DMA) engine to manipulate the operating system running on the main processor. Given additional time to investigate the matter, CTS believes it may also be possible for a hacker to install a key logger, leverage the chipset for a man-in-the-middle attack and access protected memory areas. The latter has been verified to work on a small collection of desktop motherboards, CTS says.