Tuesday morning between the hours of 12:00 am and 2:00 am EST, internet traffic to MyEtherWallet was being redirected to servers in Russia. Any users who ignored the unsigned SSL certificate warning presented when visiting the site during this time were surprised and saddened to find their Ethereum wallet drained dry.
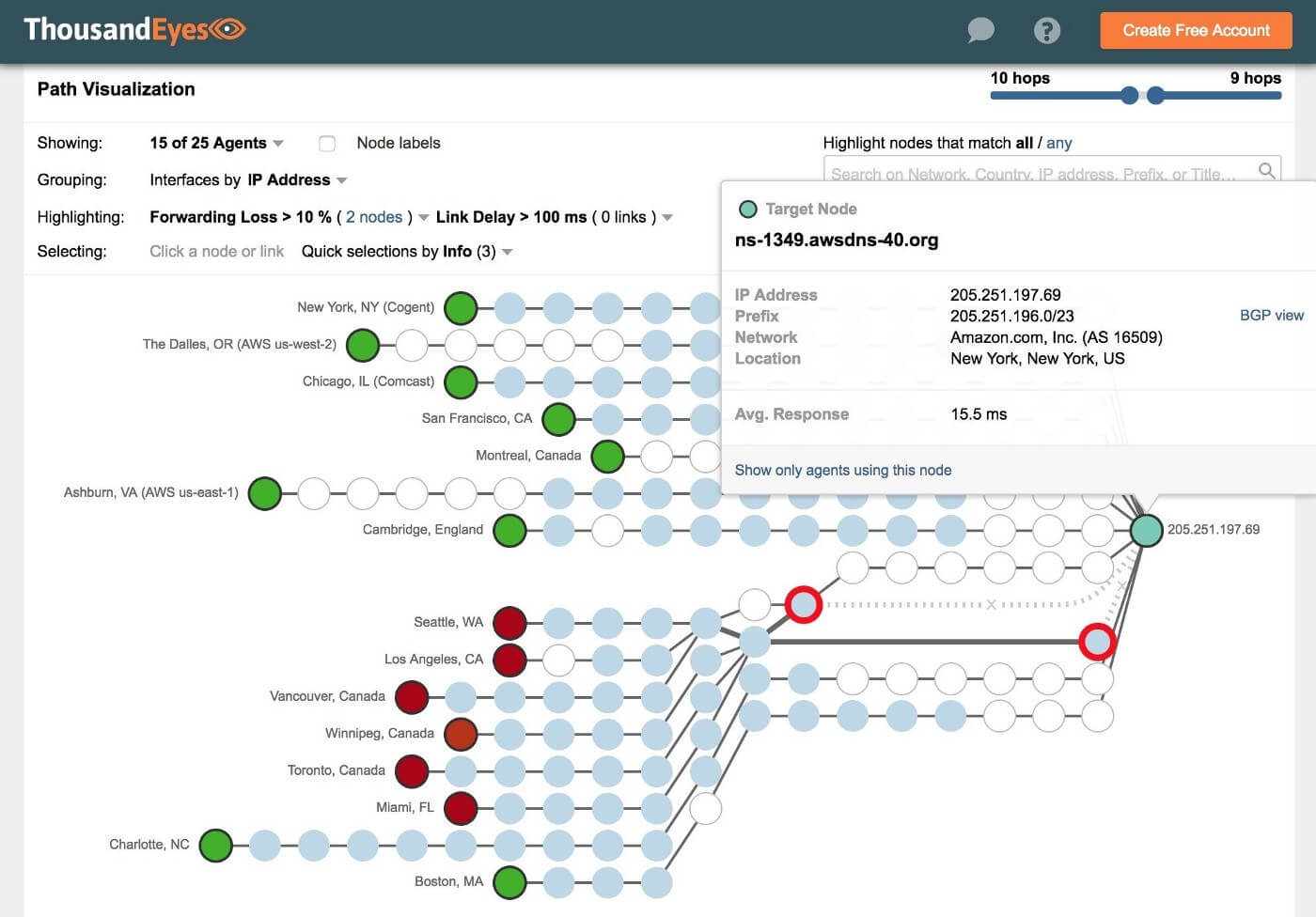
According to infosec blog Double Pulsar, the attackers hijacked a Border Gateway Protocol router near an internet exchange in Chicago to reroute DNS traffic to Amazon's Route 53 commercial cloud service. From there the hackers were able to redirect MyEtherWallet users to their bogus servers and empty their wallets. The Verge reports that at least $13,000 worth of Ethereum was stolen in the two hours that the DGP attack went unnoticed and that the attackers' wallet already contained over $17 million in the cryptocurrency.
According to an Amazon Web Services spokesperson, its DNS system was not compromised. "Neither AWS nor Amazon Route 53 were hacked or compromised," said Amazon in an email to The Register. "An upstream Internet Service Provider was compromised by a malicious actor who then used that provider to announce a subset of Route 53 IP addresses to other networks with whom this ISP was peered."
"This is the largest scale attack I have seen which combines both [DNS rerouting and BGP hijacking], and it underscores the fragility of internet security."
MyEtherWallet was not compromised directly, so only customers who visited the website during the attack were affected.
"We are currently in the process of verifying which servers were targeted to help resolve this issue as soon as possible," the company said in a statement on Reddit. "We advise users to run a local (offline) copy of the MEW (MyEtherWallet)."
So far, MyEtherWallet is the only service known to have been affected by the attack. However, it is likely other crypto-wallet websites were targeted as well.
Rerouting DNS traffic is a common tactic employed by hackers. BGP hijacking has also long been known to be a major weakness of the internet's infrastructure. However, it is not very common for both attack vectors to be used in conjunction.
According to Double Pulsar researcher Kevin Beaumont, "This is the largest scale attack I have seen which combines both [DNS rerouting and BGP hijacking], and it underscores the fragility of internet security."
While the heist was not huge (although where did that other $17 million come from), it is a lesson to those who ignore security certificate warnings. It is generally a bad idea to click "ignore" on these alerts. It is down right stupid to ignore them when you are dealing with anything having to do with your finances.
Update 4/25/18: Coindesk has reported that the hackers made off with $152,000 and TechCrunch says that the total may be as high as $365,000. These are substantially more than $13,000 The Verge came up with. The wide variances between reports is likely due to how they are being calculated.
Coindesk and The Verge looked up Ethereum transactions on Etherscan and looked at exchanges posted within the reported time frame of the attack. Variations on which transactions each news outlet considered suspect are likely to be the cause of the discrepancy.
TechCrunch's much larger figure comes from a Disqus user who has been tracking transactions and claims at least two wallets (and possibly a third) were used to receive the stolen crypto. How reliable this Disqus user, who just goes by the name "Harry," is remains questionable.
The bottom line is that until MyEtherWallet completes its investigation and releases an official figure, any amounts you read about are going to be that publication's best guess.
We will update again if any new information arrises.