What just happened? Russian hacking has skyrocketed since the country's invasion of Ukraine. The latest incident is believed to have involved cybercriminals working at the behest of Russia's foreign intelligence agency targeting diplomats at Ukrainian embassies with an ad for a cheap BMW.
According to Palo Alto Networks' Unit 42 research division (via Reuters), dozens of diplomats working in at least 22 of the roughly 80 foreign missions in Ukraine's capital, Kyiv, were targeted in the attacks.
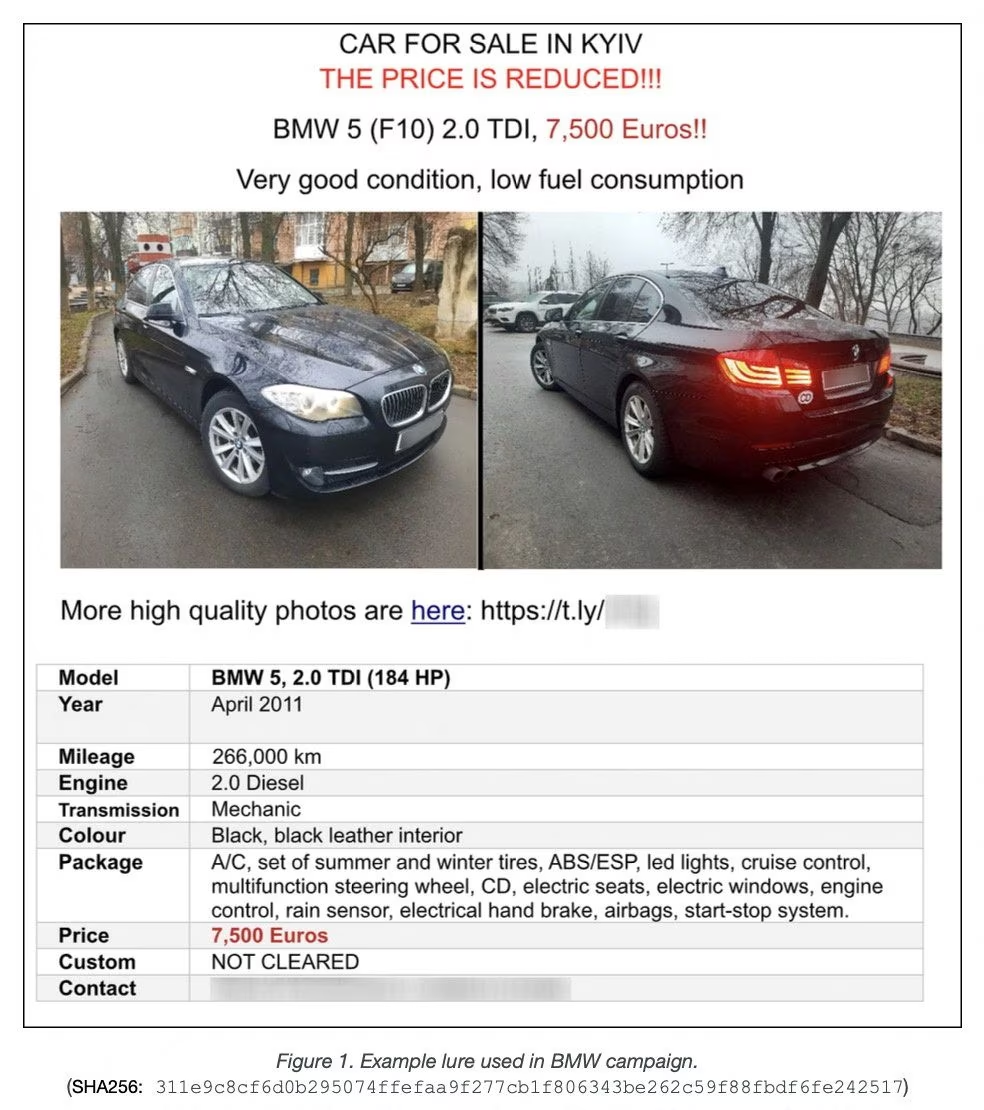
The campaign began in mid-April when a diplomat within the Polish Ministry of Foreign Affairs emailed a legitimate flyer to various embassies. The flyer was an advertisement for a used BMW 5-series sedan located in Kyiv.
The hackers then intercepted and copied the flyer, embedding it with malicious software before sending it to dozens of other diplomats in Kyiv.
The group responsible, APT29 aka "Cozy Bear," is an arm of Russia's foreign Intelligence Service (SVR). It is believed to have been behind numerous high-profile hacking incidents, including a ransomware attack on Republican National Committee third-party provider Synnex Corp, an intrusion into the Democrats' network, the hack on FireEye, and many more.
Unit 42 was able to track the altered car ad back to the SVR as the hackers re-used certain tools and techniques that had previously been connected to the spy agency.
"Diplomatic missions will always be a high-value espionage target," the Unit 42 report said. "Sixteen months into the Russian invasion of Ukraine, intelligence surrounding Ukraine and allied diplomatic efforts are almost certainly a high priority for the Russian government."
It wasn't just the addition of malicious software that Cozy Bear changed in the ad. It also listed the BMW for a lower price of 7,500 euros ($8,292). This was to make it more attractive to potential buyers who would unknowingly download the software, disguised as an album of photographs of the car, thereby allowing the attackers remote access to their devices.
A US State Department spokesperson said it was aware of the activity, and that it did not affect Department systems or accounts. The car is still for sale.
Back in March, a whistleblower leaked files from a Moscow-based defense contractor that allegedly show how the company works with Russian military and intelligence agencies to support them in hacking operations, training operatives, spreading disinformation, and scanning the internet for vulnerabilities. A month later, we saw Microsoft warn of Russian agents trying to infiltrate gaming communities.