Why it matters: Air-gapped computers, usually found in government, banking, enterprise, industrial and military setups, operate in tightly controlled environments, cut-off from the internet and under strict supervision. You'd normally think they're safe from information leaks, however an Israeli security research team has proven once again that all it takes is some creativity.
Earlier this year, a group of Israeli security researchers at the Ben Gurion University revealed novel ways in which hackers can exploit physically isolated systems to leak sensitive information. One involved manipulating display brightness to alternate between two levels for sending zeroes and ones, another was about carefully tuning the speed of the cooling fans inside a PC to create tiny vibrations that could be picked up by the accelerometer on a smartphone.
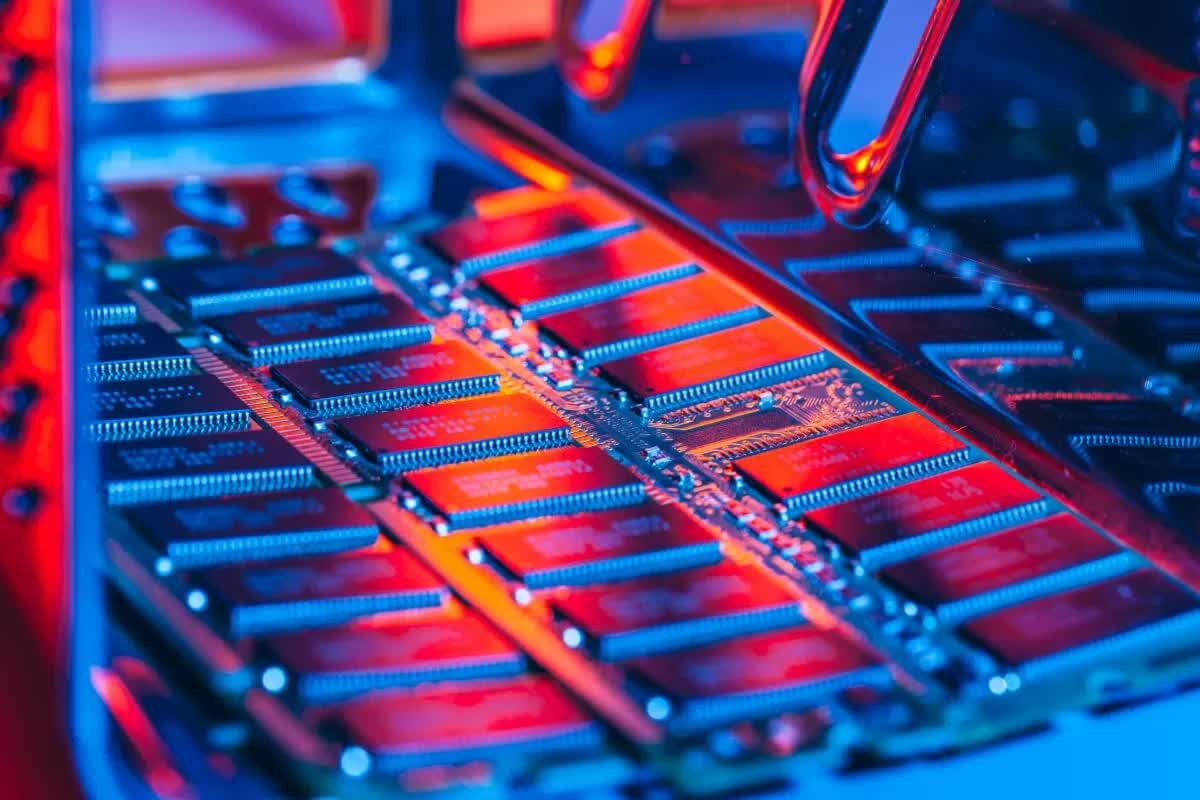
In the meantime, the team headed by Mordechai Guri found yet another quirky technique dubbed AIR-FI, which is the latest in a string of tens of projects over the last five years. Interestingly, AIR-FI uses the system memory, specifically the DDR SDRAM bus, to generate 2.4 GHz Wi-Fi signals. Sensitive information can then be leaked at rates of up to 100 bits per second to Wi-Fi receivers within a range of a few meters.
Essentially, the attack can make it so that a system isolated from public networks can broadcast Wi-Fi signals to nearby compromised devices like laptops, smartphones, smartwatches, and other IoT devices. What's worrying about this method is how the code needed to exfiltrate the sensitive information requires no special privileges to be effective, meaning attackers wouldn't need to employ complicated methods to gain access to kernel drivers or hardware resources. The code will also work in a virtual machine environment.
To perform an AIR-FI attack, a malicious actor would have to either intercept the target system to load it with malware or compromise it during the manufacturing process. Researchers point out in the paper that the easiest way to do this is via a USB drive, similar to how the Stuxnet worm made its way into supervisory control and data acquisition (SCADA) systems at uranium enrichment facilities in Iran.
The good news is that some air-gapped systems are installed in places protected to some degree against TEMPEST (Telecommunications Electronics Materials Protected from Emanating Spurious Transmissions). As for countermeasures against AIR-FI, researchers suggest that organizations deploy signal jamming through either specialized hardware equipment or a software solution that performs random memory or CPU workloads.
https://www.techspot.com/news/88037-israeli-researchers-use-ram-small-wi-fi-transmitter.html