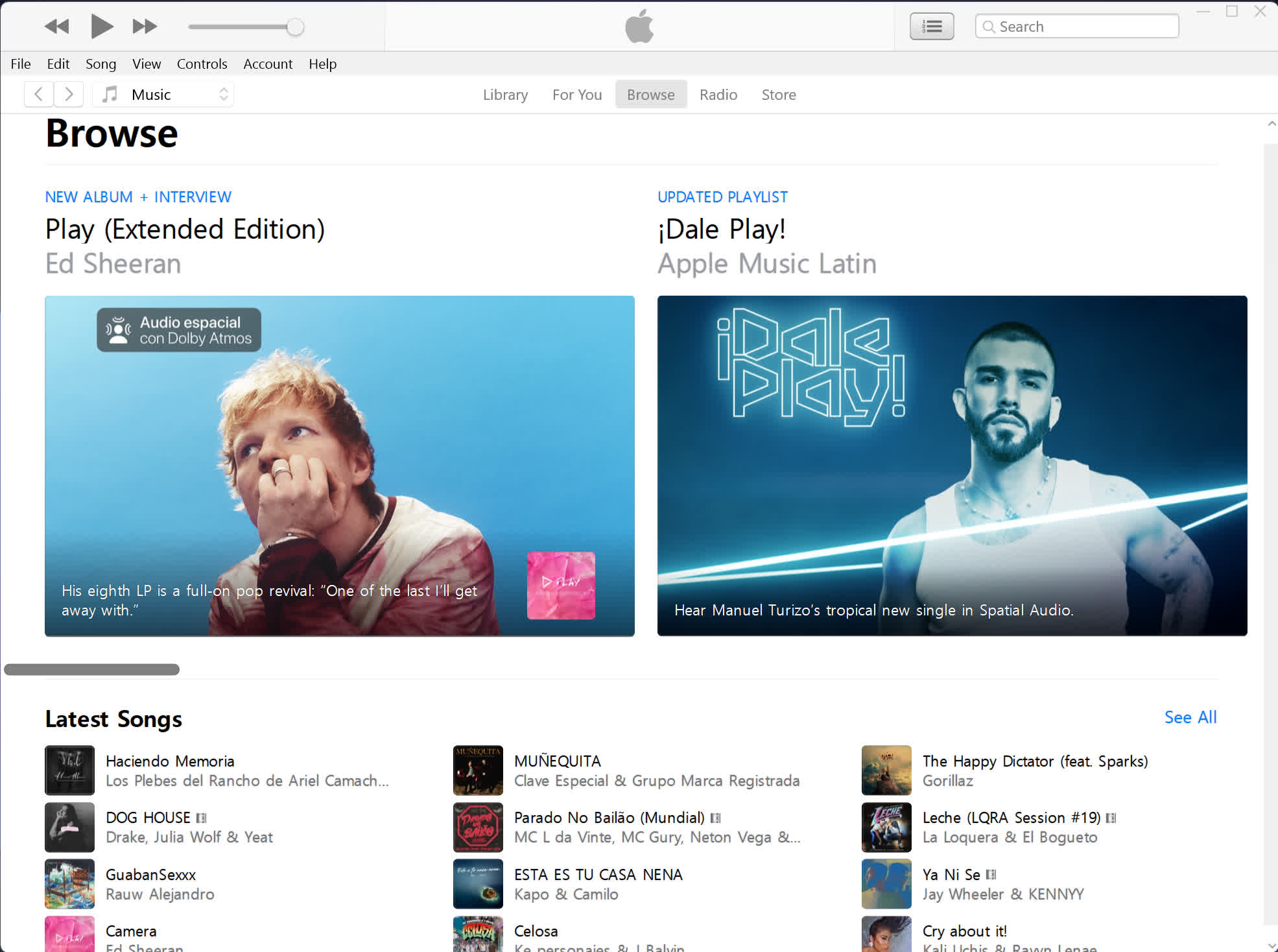
iTunes is the easiest way to enjoy everything you need to be entertained – music, movies, and TV shows – and keep it all easily organized. Rent or buy movies, download your favorite TV shows, and more. iTunes is also home to Apple Music, where you can listen to millions of songs and your entire music library. Plus, download your favorite music to listen without Wi-Fi.
Is iTunes still working in 2026?
iTunes is still fully functional in Windows. It gets regular updates and improvements with support even now. The macOS version you can still download but is no longer updated by Apple and as of macOS Catalina it has been replaced by several other services.
Why do people still use iTunes?
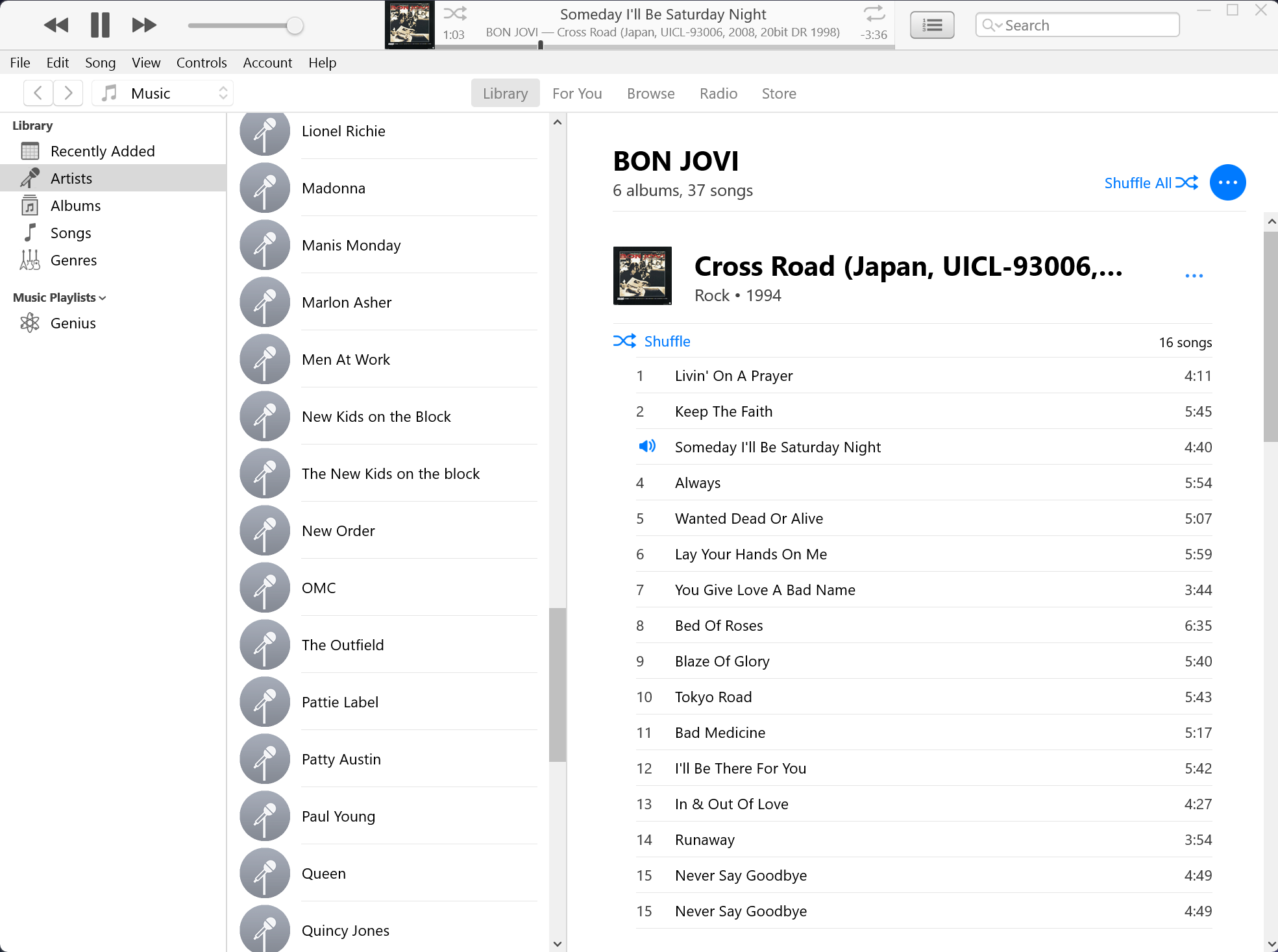
Although streaming has won a lot of the market, there are still people who would rather own the music they listen to. With apps like iTunes you get to keep the songs you have bought online or ripped.
Can I use iTunes for Windows to sync my iPhone or iPad?
Yes, iTunes allows you to sync music, photos, videos, apps, and backups between your Windows PC and iOS devices. It's especially useful if you prefer managing your device without iCloud.
What is the difference between iTunes and Apple Music?
iTunes is more of an application where you can organize your media library and buy movies, TV shows, and podcasts, whereas Apple Music is a streaming service specialized in music where you won't find movies, TV shows, or podcasts.
Features
Forget rifling through stacks of CDs or flipping through channels. iTunes puts your entire music and video collection a mere click away, giving you an all-access pass to thousands of hours of digital entertainment. Browse. Organize. Play. All from your Mac or PC.
View your library by artist, album, episode, year, rating --- any way you want. Find what you're looking for with a quick search that reveals results as you type.
Turn CDs into digital music by importing them to iTunes. Organize your entire collection with custom playlists.
Shuffle songs to mix up your groove. Listen to music from other computers on your network. Play video using onscreen controls.
iTunes can also be used to sync your content on your iPod, iPhone, and other Apple devices.
Windows 7/8 users: The last version to support Windows 8 and Windows 7 is iTunes 12.10.10.
What's New
- Adds support for iPad Pro (M5).
- Adds iOS 26 and iPadOS 26 support.
- Adds support for iPhone 17, iPhone 17 Pro, iPhone Air.
Previous release notes
This latest update adds support for the new 11-inch and 13-inch iPad Air with M2 processor, and the 11-inch and 13-inch iPad Pro with M4 processor.
This update includes security improvements and adds support for new devices.
ImageIO
- Available for: Windows 10 and later
- Impact: Processing a maliciously crafted image may lead to arbitrary code execution
- Description: This issue was addressed with improved checks.
- CVE-2021-30835: Ye Zhang of Baidu Security
- CVE-2021-30847: Mike Zhang of Pangu Lab
WebKit
- Available for: Windows 10 and later
- Impact: Processing maliciously crafted web content may lead to arbitrary code execution
- Description: Multiple memory corruption issues were addressed with improved memory handling.
- CVE-2021-30849: Sergei Glazunov of Google Project Zero