Stewart Kellar, the lawyer representing George Hotz, also known as GeoHot, said he would challenge San Francisco District Court Judge Susan Illston's court order for his client to hand over his computers to Sony next week. The Temporary Restraining Order (TRO) was given to stop GeoHot from putting information on the Web about his PlayStation 3 hack.
"The information sought at issue is less than 100 kilobytes of data. Mr. Hotz has terabytes of storage devices," Kellar told Wired. "Impounding his computers, it's like starting a forest fire to cut down a single tree." GeoHot has already removed the code from his website and YouTube, but Kellar will petition Illston to reconsider other parts of the TRO, specifically regarding giving Sony his equipment and retrieving every instance of his code. "Mr. Hotz can't retrieve the Internet," Kellar said.
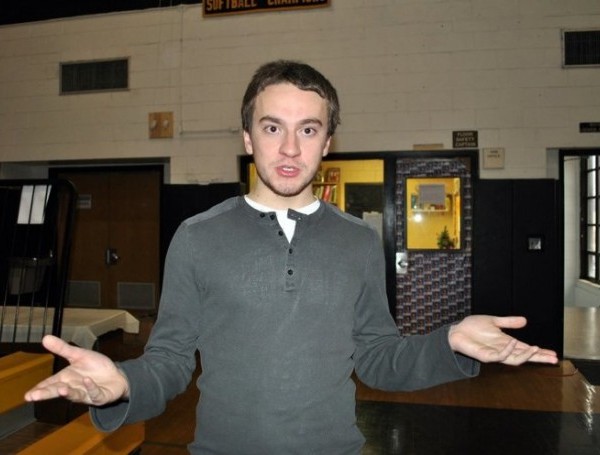
Sony has specifically requested that the 21-year-old surrender "any and all computer hardware and peripherals containing circumvention devices, technologies, programs, parts thereof, or other unlawful material, including but not limited to code and software, hard disc drives, computer software, inventory of CD-ROMS, computer diskettes, or other material containing circumvention devices, technologies, programs, parts thereof, or other unlawful material." Illston ruled that the defendant "shall retrieve" code "which he has previously delivered or communicated."
Sony's legal attacks against the hackers that released the PlayStation 3 root key and custom firmware began last month. Sony is targeting 100 members of the fail0verflow hacker collective who found security codes for the PS3, as well as GeoHot who independently found and published the PS3 root key.