Google Chrome is a fast, simple, and secure web browser, built for the modern web. Chrome combines a minimal design with sophisticated technology to make the web faster, safer, and easier. Google builds powerful tools that help you connect, play, work and get things done. And all of it works on Chrome.
Is Google Chrome safe and private?
The Chrome browser utilizes site isolation, sandboxing, and predictive phishing protections to keep your browsing secure, among others. However, Google's browser always raises privacy concerns due to the fact that everything you do in Chrome, including every character you type into the address bar, is recorded by Google and linked to you. While using other Google services, all that data may be cross-referenced.
More privacy-conscious users may prefer to use Firefox or other Chromium-based alternatives (that may or may not record as much data) or try Ungoogled Chromium.
Is Chrome the fastest browser?
Chrome, Firefox, Safari and other major browsers are updated every few weeks, so it's hard to compare them over time which is the fastest. Chrome is known to be a RAM hog, but when used heavily, other browsers are known to be just as resource-consuming.
Google is good at creating the illusion of speed with prediction algorithms that preload parts of web pages that you are likely to visit. With a minimalistic design, you'll feel at home with Chrome, plus built-in integration with other Google services and mobile browsing can also be very convenient.
What are the best Chrome alternatives?
There are tons of good and free alternatives for browsing the web. If you want a more private browsing, you can opt for Firefox or Brave. If you don't want to use Google services, you can use Ungoogled Chromium.
Opera, Microsoft Edge and Vivaldi are other great options, these last two are Chromium-based just like Google Chrome.
What are the best features of Chrome?
Chrome is the most popular web browser out there, so website compatibility with it and other Chromium-based browsers is top notch. Performance is usually perceived as good (see question above).
Chrome is also feature-filled but not bloated. It does integrate nicely with other Google services and also lets you sync browsing history and bookmarks with your phone and other devices. Finally, Chrome has a vast library of extensions to add capabilities to your browser experience.
Features
Speed
Chrome is designed to be fast in every possible way: It's quick to start up from your desktop, loads web pages in a snap, and runs complex web applications fast. Learn more about Chrome and speed.
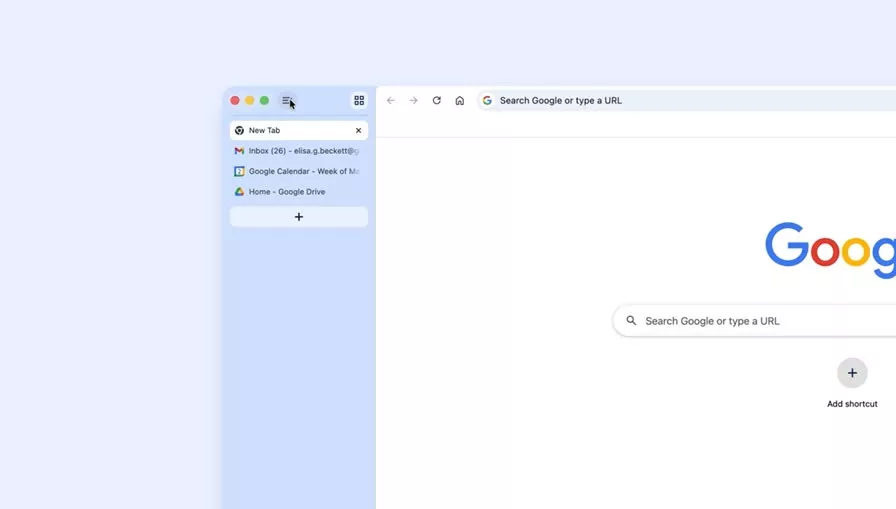
Stay organized with tabs
Tabs help you stay organized, keep track of multiple pages, and multi-task. You can group tabs together for better organization or pin tabs to automatically open websites you use the most.
What's New
The Stable channel has been updated to 148.0.7778.178/179 for Windows/Mac and 148.0.7778.178 for Linux, which will roll out over the coming days/weeks. A full list of changes in this build is available in the Log.
Security changes will be updated shortly.
Previous Release Notes:
Security Fixes and Rewards
Note: Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven't yet fixed.
This update includes 30 security fixes. Below, we highlight fixes that were contributed by external researchers. Please see the Chrome Security Page for more information.
- [$7000][494352590] Critical CVE-2026-7363: Use after free in Canvas. Reported by heapracer on 2026-03-19
- [TBD][493221953] Critical CVE-2026-7361: Use after free in iOS. Reported by Google on 2026-03-16
- [TBD][503419515] Critical CVE-2026-7344: Use after free in Accessibility. Reported by Google on 2026-04-16
- [TBD][503645680] Critical CVE-2026-7343: Use after free in Views. Reported by Google on 2026-04-17
- [$16000][493955227] High CVE-2026-7333: Use after free in GPU. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-19
- [TBD][495852034] High CVE-2026-7360: Insufficient validation of untrusted input in Compositing. Reported by Google on 2026-03-24
- [TBD][496284494] High CVE-2026-7359: Use after free in ANGLE. Reported by Google on 2026-03-25
- [TBD][496285281] High CVE-2026-7358: Use after free in Animation. Reported by Google on 2026-03-25
- [TBD][496456528] High CVE-2026-7334: Use after free in Views. Reported by Batuhan Eşref KOÇ on 2026-03-26
- [TBD][497047552] High CVE-2026-7357: Use after free in GPU. Reported by Google on 2026-03-27
- [TBD][497769116] High CVE-2026-7356: Use after free in Navigation. Reported by Google on 2026-03-30
- [TBD][498746519] High CVE-2026-7354: Out of bounds read and write in Angle. Reported by Google on 2026-04-01
- [TBD][498809718] High CVE-2026-7353: Heap buffer overflow in Skia. Reported by Google on 2026-04-01
- [TBD][499023054] High CVE-2026-7352: Use after free in Media. Reported by Google on 2026-04-02
- [TBD][499119490] High CVE-2026-7351: Race in MHTML. Reported by Google on 2026-04-02
- [TBD][500018484] High CVE-2026-7350: Use after free in WebMIDI. Reported by Google on 2026-04-06
- [TBD][500034684] High CVE-2026-7349: Use after free in Cast. Reported by Google on 2026-04-06
- [TBD][500104917] High CVE-2026-7348: Use after free in Codecs. Reported by Google on 2026-04-06
- [TBD][500387779] High CVE-2026-7335: Use after free in media. Reported by Jungwoo Lee (@physicube) and Wongi Lee (@_qwerty_po) on 2026-04-07
- [TBD][500767595] High CVE-2026-7336: Use after free in WebRTC. Reported by Mozilla on 2026-04-09
- [TBD][500880819] High CVE-2026-7337: Type Confusion in V8. Reported by [email protected] on 2026-04-09
- [TBD][501722605] High CVE-2026-7347: Use after free in Chromoting. Reported by Google on 2026-04-11
- [TBD][502206907] High CVE-2026-7346: Inappropriate implementation in Tint. Reported by Google on 2026-04-13
- [TBD][502248774] High CVE-2026-7345: Insufficient validation of untrusted input in Feedback. Reported by Google on 2026-04-13
- [TBD][502449857] High CVE-2026-7338: Use after free in Cast. Reported by Krace on 2026-04-14
- [TBD][503889643] High CVE-2026-7342: Use after free in WebView. Reported by Google on 2026-04-17
- [TBD][504586599] High CVE-2026-7341: Use after free in WebRTC. Reported by Google on 2026-04-20
- [$4000][493957495] Medium CVE-2026-7339: Heap buffer overflow in WebRTC. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-19
- [$3000][497896137] Medium CVE-2026-7340: Integer overflow in ANGLE. Reported by 86ac1f1587b71893ed2ad792cd7dde32 on 2026-03-30
- [TBD][498285711] Medium CVE-2026-7355: Use after free in Media. Reported by Google on 2026-03-31
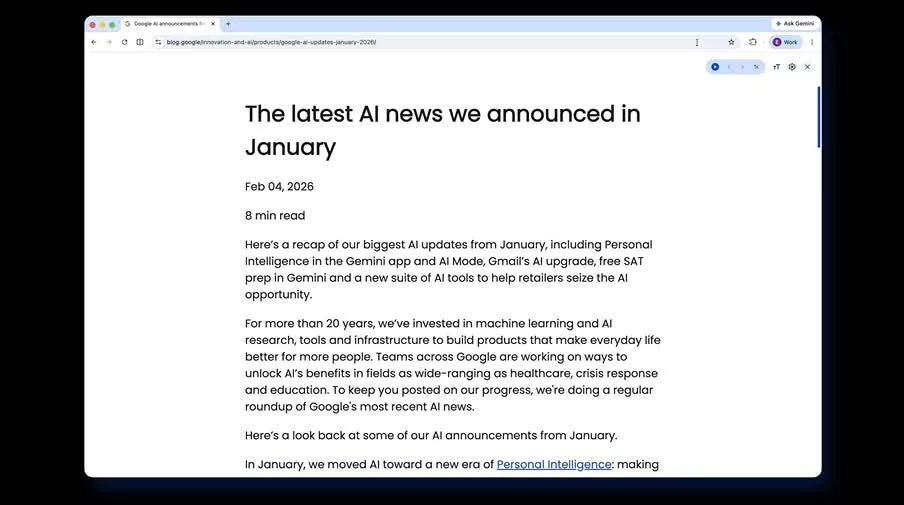
Get more done with new vertical tabs and immersive reading mode in Chrome
Today we are beginning to roll out two new features designed to streamline your browser and help you maximize productivity in Chrome.
You now have the option to use vertical tabs in Chrome, depending on your preferences. Just right click on any Chrome window and select "Show Tabs Vertically." By moving your tabs to the side of your browser window, you can read full page titles and manage tab groups with ease – even when your tab count hits double digits. This layout is perfect for multitasking, saving you time by making sure you never lose a tab.
And reading mode, a favorite Chrome feature for deep focus, is even better with a new full-page interface. Right-click on any page and select "Open in reading mode" to remove visual distractions and transform a busy webpage into an immersive, text-focused reading experience.
Chrome 146.0.7680.177/178 changelog
The Stable channel has been updated to 146.0.7680.177/178 for Windows/Mac and 146.0.7680.177 for Linux, which will roll out over the coming days/weeks. A full list of changes in this build is available in the Log
Security Fixes and Rewards
Note: Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven't yet fixed.
This update includes 21 security fixes. Please see the Chrome Security Page for more information.
- [TBD][493952652] High CVE-2026-5273: Use after free in CSS. Reported by Anonymous on 2026-03-18
- [TBD][491732188] High CVE-2026-5272: Heap buffer overflow in GPU. Reported by inspector-ambitious on 2026-03-11
- [TBD][488596746] High CVE-2026-5274: Integer overflow in Codecs. Reported by heapracer (@heapracer) on 2026-03-01
- [TBD][489494022] High CVE-2026-5275: Heap buffer overflow in ANGLE. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-04
- [TBD][489711638] High CVE-2026-5276: Insufficient policy enforcement in WebUSB. Reported by Ariel Simon on 2026-03-04
- [TBD][489791424] High CVE-2026-5277: Integer overflow in ANGLE. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-05
- [TBD][490254128] High CVE-2026-5278: Use after free in Web MIDI. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-06
- [TBD][490642836] High CVE-2026-5279: Object corruption in V8. Reported by Hyeonjun Ahn (@_deayzl) on 2026-03-08
- [TBD][491515787] High CVE-2026-5280: Use after free in WebCodecs. Reported by heapracer (@heapracer) on 2026-03-11
- [TBD][491518608] High CVE-2026-5281: Use after free in Dawn. Reported by 86ac1f1587b71893ed2ad792cd7dde32 on 2026-03-10
- [TBD][491655161] High CVE-2026-5282: Out of bounds read in WebCodecs. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-11
- [TBD][492131521] High CVE-2026-5283: Inappropriate implementation in ANGLE. Reported by sweetchip on 2026-03-12
- [TBD][492139412] High CVE-2026-5284: Use after free in Dawn. Reported by 86ac1f1587b71893ed2ad792cd7dde32 on 2026-03-12
- [TBD][492228019] High CVE-2026-5285: Use after free in WebGL. Reported by c6eed09fc8b174b0f3eebedcceb1e792 on 2026-03-13
- [TBD][493900619] High CVE-2026-5286: Use after free in Dawn. Reported by sweetchip on 2026-03-18
- [TBD][494644471] High CVE-2026-5287: Use after free in PDF. Reported by Syn4pse on 2026-03-21
- [NA][495507390] High CVE-2026-5288: Use after free in WebView. Reported by Google on 2026-03-23
- [NA][495931147] High CVE-2026-5289: Use after free in Navigation. Reported by Google on 2026-03-25
- [NA][496205576] High CVE-2026-5290: Use after free in Compositing. Reported by Google on 2026-03-25
- [TBD][490118036] Medium CVE-2026-5291: Inappropriate implementation in WebGL. Reported by heapracer (@heapracer) on 2026-03-06
- [NA][492213293] Medium CVE-2026-5292: Out of bounds read in WebCodecs. Reported by Google on 2026-03-12
- Google is aware that an exploit for CVE-2026-5281 exists in the wild.
Google Chrome adds split view, PDF annotations, and Drive saves
Google is making Chrome a little more work-friendly with a trio of productivity upgrades that are now rolling out on the desktop. The browser's new built-in split view lets you run two tabs side by side without juggling windows, while its PDF viewer can now handle highlights, notes, and even signatures.
There's also a smarter Save to Google Drive option that sends PDFs straight into a dedicated "Saved from Chrome" folder, cutting out the download-and-reupload dance. If you live in your browser all day, the latest Chrome update is worth grabbing.
The Stable channel has been updated to 145.0.7632.109/110 for Windows/Mac and 144.0.7559.109 for Linux, which will roll out over the coming days/weeks. A full list of changes in this build is available in the Log.
Security Fixes and Rewards
Note: Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven't yet fixed.
This update includes 3 security fixes. Please see the Chrome Security Page for more information.
- [TBD][477033835] High CVE-2026-2648: Heap buffer overflow in PDFium. Reported by soiax on 2026-01-19
- [TBD][481074858] High CVE-2026-2649: Integer overflow in V8. Reported by JunYoung Park(@candymate) of KAIST Hacking Lab on 2026-02-03
- [N/A][476461867] Medium CVE-2026-2650: Heap buffer overflow in Media. Reported by Google on 2026-01-18
We would also like to thank all security researchers that worked with us during the development cycle to prevent security bugs from ever reaching the stable channel.
Many of our security bugs are detected using AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, or AFL.
Features
Chrome 144 is rolling out now, and this post shares some of the key features from the release. Highlights from this release:
- Highlight find-in-page search text with a new pseudo-element.
- Request permission to use location date with the geolocation element
- The Temporal API brings a modern date and time API to the web.
The ::search-text pseudo-element
Exposes find-in-page search result styling as the ::search-text pseudo-element, which is a highlight pseudo-element like those used for selection and spelling errors. This lets you change the foreground and background colors or add text decorations. This is especially useful if the browser defaults have insufficient contrast with the page colors or are otherwise unsuitable.