Why it matters: After exploring the possibility of using cloud services for work exclusively, there is only one possible conclusion: it is a giant pain. There are only very specific types of businesses and individuals that can go to fully cloud-based solutions for file sharing.

With the introduction of the European Union’s GDPR, international businesses have even more reason to keep tight control over their stored data to avoid hefty fines. Businesses have taken different approaches to maintaining proper security. Some such as IBM have banned USB drives in attempt to avoid the spread of malware. Others have implemented stricter rules for Bring Your Own Device policies.
Faced with the different alternatives on my day job, I was tasked with testing two of Kingston’s encrypted flash drives to see how well they work on a day to day basis compared to the option of using cloud services exclusively. Using encrypted drives with the capability to be used in a read-only fashion allows for secure file transfer between offline devices and network machines being regularly used.
Kingston's DataTraveler Vault Privacy 3.0 and IronKey D300 both offer out of the box hardware encryption. The Vault Privacy 3.0 uses 256-bit AES hardware encryption in XTS mode to achieve FIPS 197 certification. The IronKey D300 goes a step further and has physical resistance to data thieves with a zinc casing and has an epoxy fill that shows if any physical tampering attempts were made. Upgrades to physical defenses combined with the same 256-bit AES hardware encryption give the D300 its FIPS 140-2 Level 3 certification.

Medical, legal, and government agencies’ needs for compliance are all met by both of these drives. For enterprise, there are fully managed versions available with remote wiping capabilities and secondary passwords for administrative use in case someone forgets their password or is terminated and refuses to give up their credentials.
For the careless and accident prone users, both drives are IPX8 rated for submersion in water up to four feet deep. The Vault Privacy has a slot for a ring strap to be put through and the D300 has an included steel cable with a threaded connector so that there is no chance of it falling off of a key ring or lanyard.

Upon inserting Kingston's encrypted USB drives, a CDFS partition appears with an unlocking tool. Users are required to enter their password before the main formatted partition of the drive is visible. Windows, Mac, and Linux software support is available. Passwords on the DataTraveler Vault Privacy 3.0 must be between 8 and 16 characters with a combination of alphanumeric and symbolic characters. The IronKey D300 allows the end user a little more freedom of choice.
Performance
One of the caveats of an encrypted drive is that all file transfers are impacted by the encryption process. Both the Vault Privacy 3.0 and IronKey D300 are rated at 250 MB/s read and 40 MB/s write for the 32GB model when using USB 3.0.
In day to day use, I have found that any slow down due to encryption is largely unnoticeable. Without looking at benchmarks, there is not a noticeable difference in regular use. Whether you are working with large quantities of small files or large continuous files, the drives still perform about on par with unsecured USB devices.
Prolonged reads and writes to the drives went smoothly as well. Large files do cause the drives to warm up a little bit, but certainly not to the point of concern. The metal casing on the D300 helps dissipate what little heat it does produce while the DataTraveler only starts to really throttle after nearly filling the entire drive. In regular use, thermal throttling is unlikely to ever be a problem.
One thing to note is that both drives are formatted as FAT32 out of the box. While using FAT32 does give widespread compatibility with almost any device, exFAT and NTFS allow for contiguous files larger than 4GB to be transferred. There is no meaningful performance difference when using different file system types.
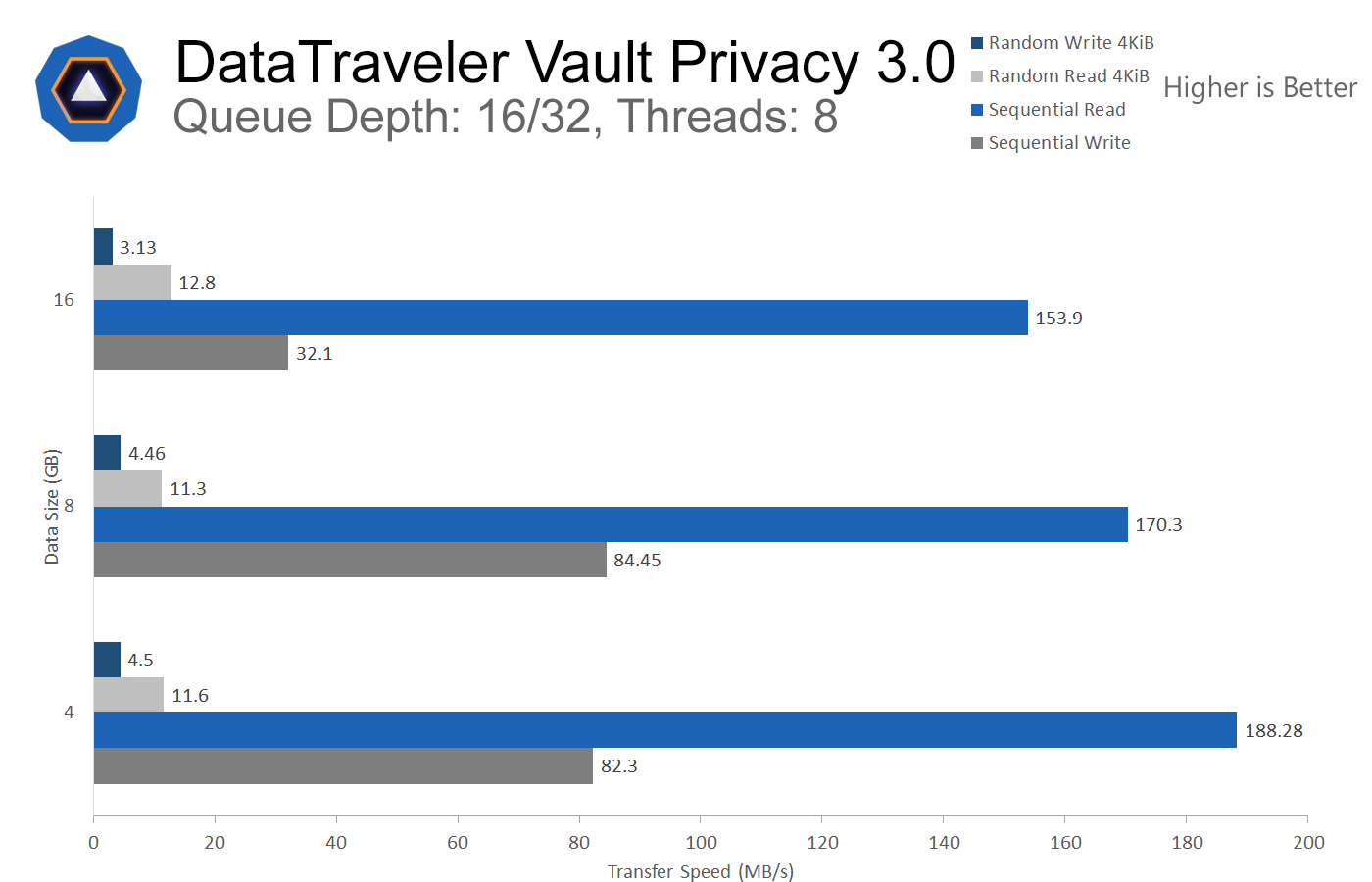
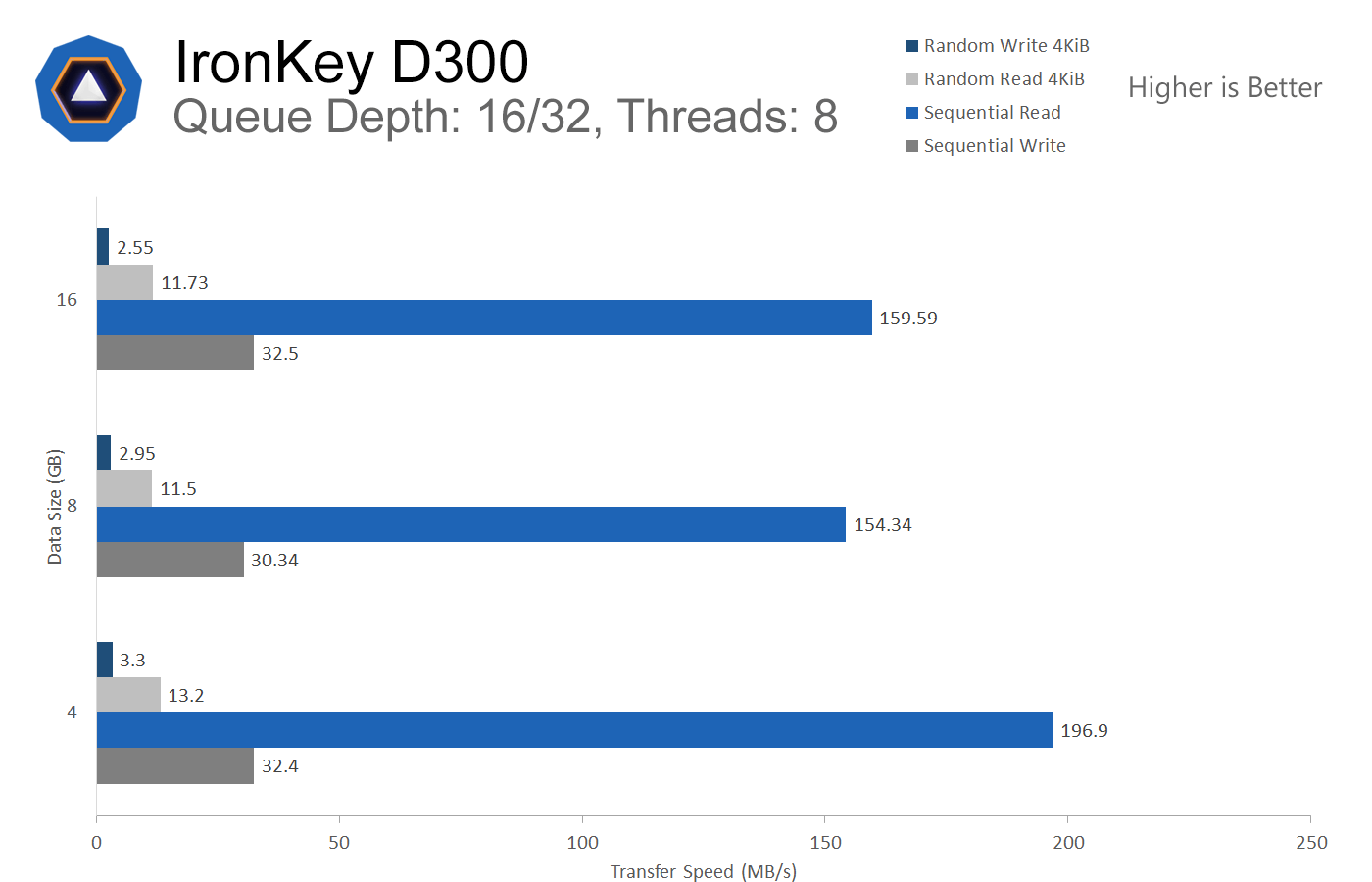
All of that aside, here are the raw numbers from CrystalDiskMark. These benchmarks were run on a mid-range laptop so as to showcase what regular users will actually see in the real world. It is certainly possible to get better numbers, but I still exceeded Kingston’s ratings in some of the tests, so it is safe to say that their specs are a fair average of what one can expect. Sequential and Random tests were run using a single queue and thread. In a second round, each drive was benchmarked using 16 queues in sequential tests and 32 queues for random with 8 threads in both sequential and random trials.
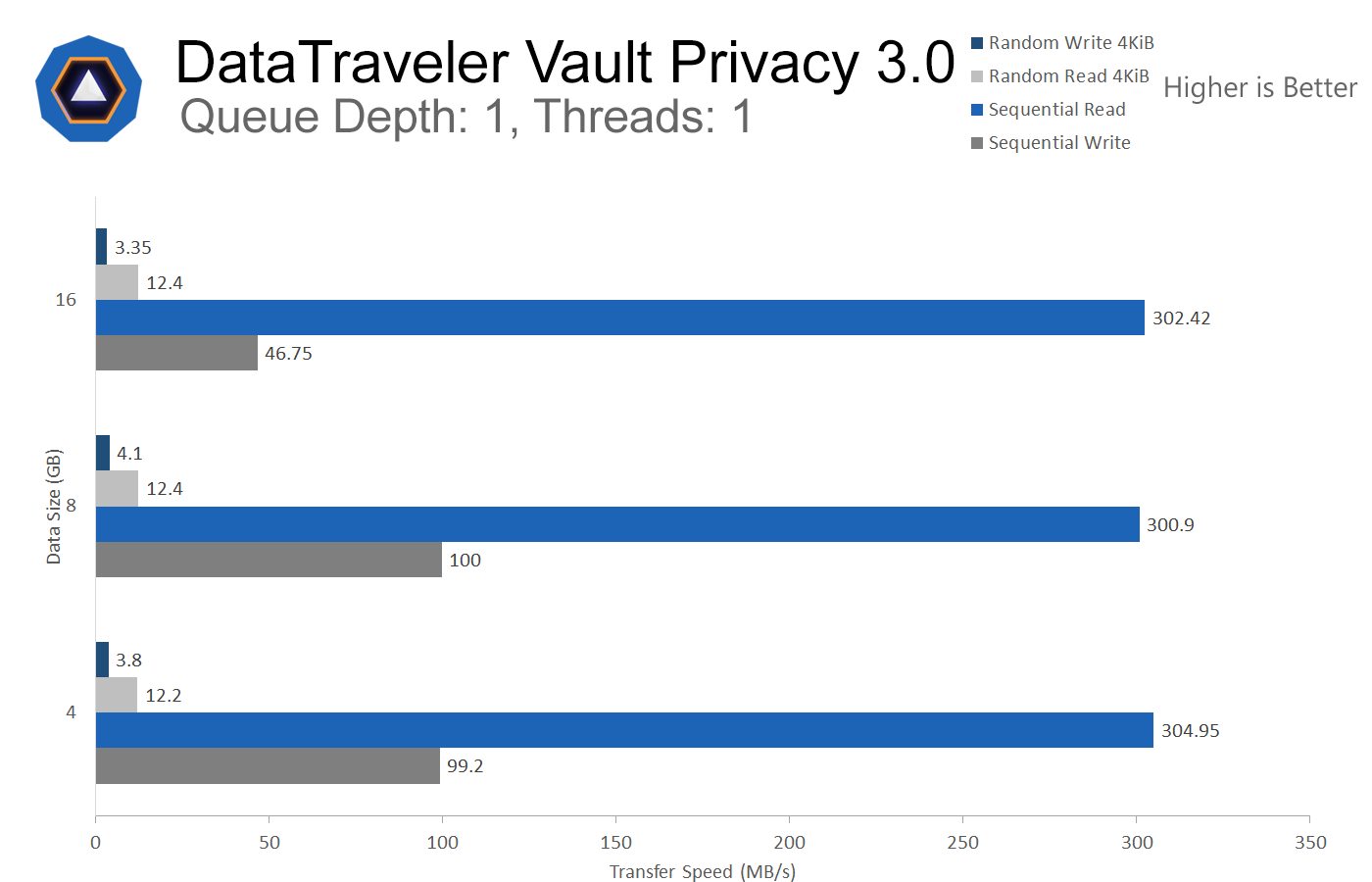
The DataTraveler Vault Privacy 3.0 well exceeds Kingston's specifications when working with smaller files. Only once the 16GB test is run do the speeds begin to really drop off and provide the expected performance metrics.
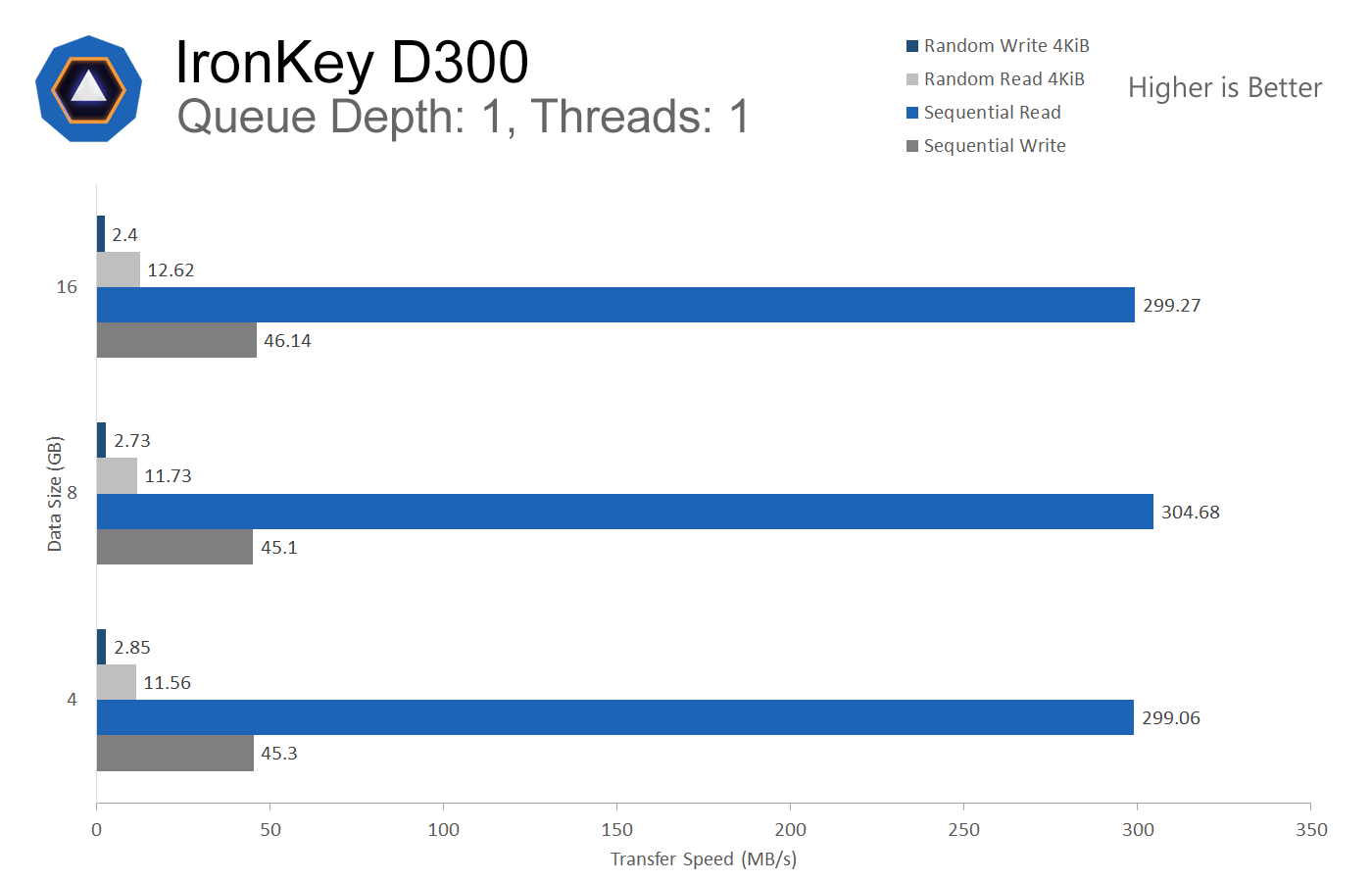
As expected, the D300 performs almost exactly the same as the Vault Privacy 3.0. There is absolutely no noticeable difference in real world performance between the two. Copying a combination of media files, documents, and program folders to the drives produced no significant differences.
Ease of Use
In any security system, people are often the weakest point. For all removable drives, manufacturers recommend using safely remove hardware option. Kingston’s software has its own safe shutdown option to ensure that the drive’s internal hardware correctly closes out all file streams and closes the USB connection to the host computer.
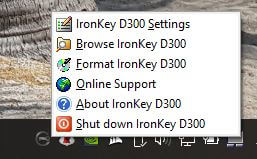
How many people will actually bother to safely remove a USB stick each and every single time they need to use one? The answer to that is probably not very many. At least I know I am guilty of almost never using safe removal. Fortunately, both the DataTraveler and D300 do have driver support for quick removal. All data will remain securely encrypted in the event of a premature drive removal. In my experience, both encrypted drives work just fine with quick removal so long as you make sure any file transfers are complete. Kingston still recommends you use their own software safe shutdown option, but I digress.
Unfortunately, it is not possible to use the D300 and DataTraveler with every device that a standard flash drive can be used with. You must have a device running Windows, Mac OS, or Linux. Plugging either of the drives into a device running Android, iOS, a proprietary OS, or no operating system will not work because the software on the CDFS partition cannot launch and therefore you cannot access or store any data on the drive.
This issue is recognized and there is actually another product to solve that problem. The DataTraveler 2000 drive has a physical keypad that allows it to be unlocked before plugging it into a device. Projectors, lab equipment, or devices that do not support the D300 and DataTraveler can still make use of the DataTraveler 2000. Although I have not tried that drive personally, it is meant to be as secure as the Vault Privacy 3.0 carrying the same FIPS 197 certification.

After becoming quite familiar with these two drives, I can safely conclude that the experience is mostly seamless provided you are using regular laptops or desktops. There are some minor hurdles to get over such as remembering to unlock the drive each time you plug it in before you try to save a document to it, but it did not take long to become accustomed to. AutoPlay can be used to automatically launch the unlocking software, but anyone seeking enhanced security should know that AutoPlay being enabled is a horrible idea.
Comparison to cloud alternatives
The first issue encountered with cloud-only solutions is trying to transfer files between offline devices and workstations. Standalone machines being used for single tasks such as controlling a piece of equipment cannot be accessed in any way other than direct physical access. Adding internet access puts legacy applications running on out of date operating systems at high risk of being compromised.
Instead of spending a small fortune trying to retrofit proprietary equipment with newer operating systems that can securely access cloud services, implementing controlled device policies are a much better solution. So long as every device being used on a network is accounted for and properly protected, there is little risk involved. The read-only mode on Kingston’s encrypted drives is a highly underrated feature.
One aspect where the cloud wins every time is overall scalability. If you need to deal with very large data sets, a removable drive of any kind is not going to be the ideal choice. DataTraveler models only reach 64GB and the IronKey D300 only scales up to 128GB of storage.

Cloud storage is significantly cheaper on a per-gigabyte basis and can scale infinitely for most businesses. Software encryption can also be performed before uploading files to the cloud making for a seamless experience. Arguably, software encryption may not be technically as secure as hardware approaches. Even though hardware encryption exists for hard drives as well, the data still needs a secure upload method before reaching cloud drives.
When you want to share files with someone else via the cloud, a link can easily be generated and sent to an email address or phone number so that only that person may access shared data. Sharing data via USB can be more convenient when in close proximity or when internet access is unavailable, but clearly is not as useful when on opposite sides of the world.
Due to the requirement of internet access for cloud storage, file transfer speeds can only be as good as your internet service provider allows for. Some businesses can afford to install impressively fast connections, but employees outside the office are subject to whatever Wi-Fi or paid LTE with data caps can provide. Going back to performance figures, encrypted flash drives are currently likely to offer better performance than uploading and downloading from cloud hosts.
When time is a crucial factor, using local means of storage will almost always provide a better experience. Unfortunately though, local hardware can fail and may not be backed up with multiple redundant copies of data. Kingston backs their encrypted drives with 5-year warranties showing that failure is unlikely, but it can and will happen on occasion.
Closing remarks
When looking at different methods of increasing security for your network, banning all USB devices can be more of a pain than an actual benefit. In most instances, the knee-jerk reaction to place sweeping bans on removable devices only leads to headaches and wasted time trying to find workarounds of how to move data from point A to point B without inserting removable storage.

During my time using the DataTraveler Vault Privacy 3.0 and IronKey D300, I have found that it is possible to become accustomed to using a password protected USB drive. It may not be quite as convenient to enter a password every time you insert a removable storage device, but the added security is certainly worth it if you are carrying around sensitive information. Even non-technical users can easily make use of hardware encryption.
Pricing on the drives is too high for average consumers. Kingston’s encrypted drives are very clearly being marketed to larger businesses and government agencies. It would be nice to see storage capacities go up and pricing come down to more reasonable levels so that they are more accessible to regular consumers.
All of that said, would I recommend the drives for personal use? Maybe. If cost were truly not a point of consideration, I would have no problem giving the D300 my recommendation for its excellent build quality and respectable performance. It is by far the sturdiest removable drive I have ever used. For businesses that would rather invest in security as opposed to crisis PR teams and lawyers following a data breach, either of these drives can provide a turnkey solution that simply works.