Why it matters: Earlier this week, researchers from Blackberry and Intezer released information on a hard-to-detect Linux malware targeting Latin American financial institutions. Known as Symbiote, the threat provides unauthorized users with the ability to harvest credentials or assume remote access to the target machine. Once infected, all malware is hidden and rendered undetectable.
Intezer's Joakim Kennedy and the Blackberry Research and Intelligence Team discovered that the threat presents as a shared object library (SO) rather than a typical executable file that users must run to infect a host. Once infected, the SO is loaded into currently running processes on the target machine.
The infected computers provide threat actors with the ability to harvest credentials, leverage remote access capabilities, and execute commands with otherwise unauthorized elevated privileges. The malware is loaded before any other shared objects via the LD_PRELOAD directive, allowing it to avoid detection. Being loaded first also allows the malware to leverage other loaded library files.
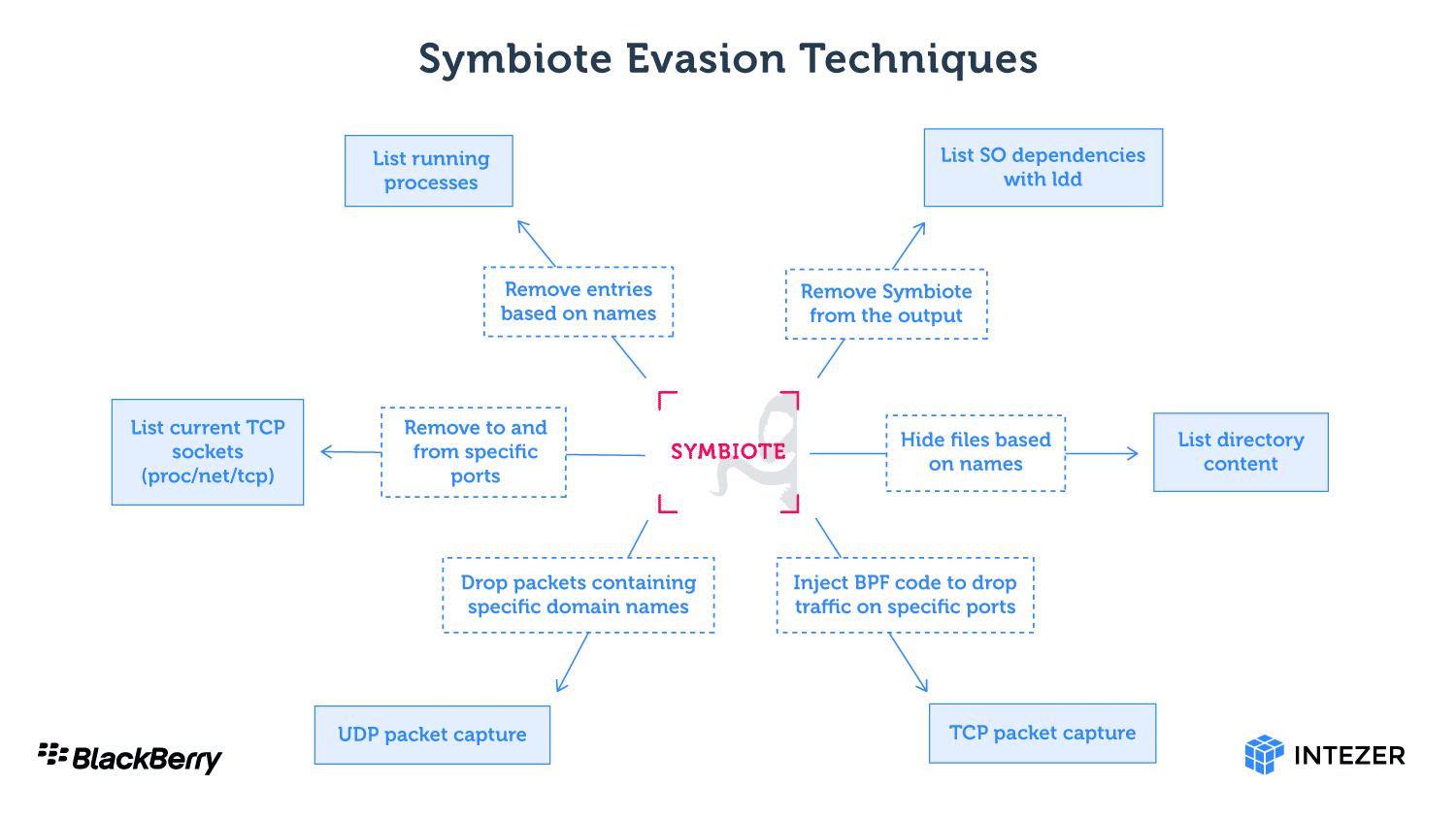
In addition to the actions described above, Symbiote can hide the infected machine's network activity by creating specific temp files, hijacking infected packet filtering bytecode, or filtering UDP traffic using specific package capture functions. The Blackberry and Intezer blogs provide in-depth explanations of each method if you're into the technical details.
The team first detected the threat in Latin American-based financial institutions in 2021. Since then, the team has determined that the malware shares no code with any other known malware, classifying it as a completely new malware threat to Linux operating systems. While the new threat is designed to be hard to find, admins can use network telemetry to detect anomalous DNS requests. Security analysts and system administrators can also use statically linked antivirus (AV) and endpoint detection and response (EDR) tools to ensure userland level rootkits do not infect target machines.