AI Agents Explained: The Next Evolution in Artificial Intelligence
Interacting with AI chatbots like ChatGPT can be fun and sometimes useful, but the next level of everyday AI goes beyond answering questions: AI agents carry out tasks for you.
GPUs vs. FPGAs: What's the Difference?
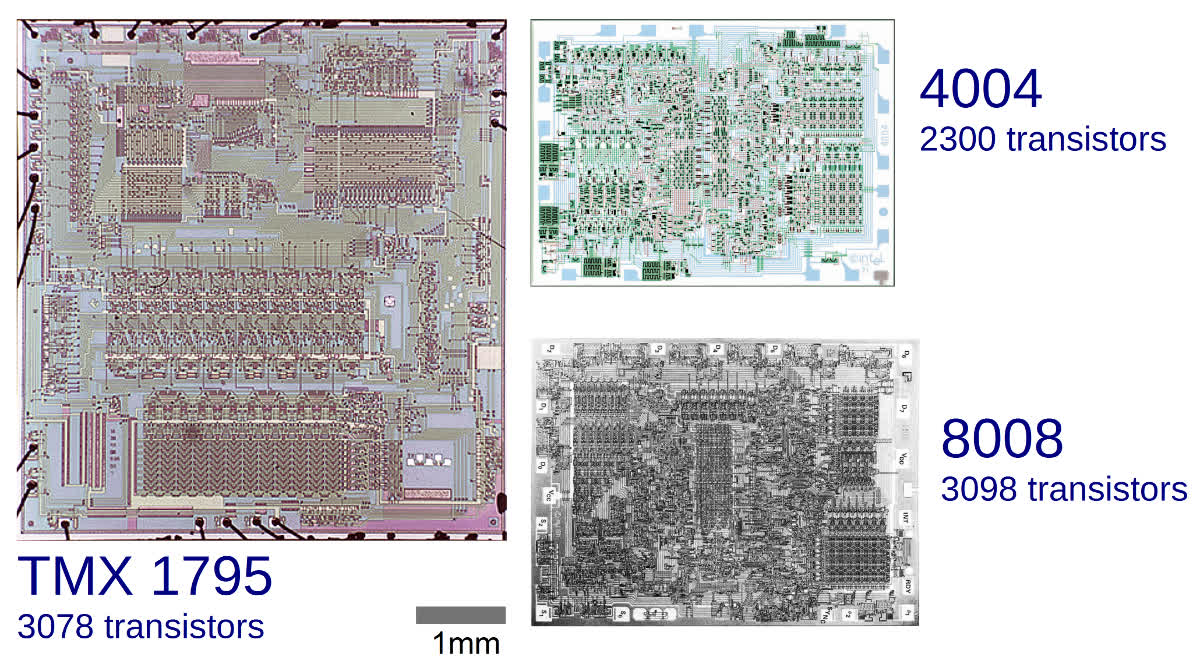
50 Years Later: The Revolutionary 8008 Microprocessor
#TBT Intel's groundbreaking 8008 microprocessor was produced over 50 years ago, the ancestor of the x86 processor family that you may be using right now. While the 8008 wasn't the first microprocessor, it was truly revolutionary, triggering a revolution and leading to the x86 architecture that dominated personal computers for decades to come.
The complete list of alternatives to all Google products
Why Incognito Mode and Private Browsing are Not Private
Are you expecting to have complete privacy when you enable incognito mode or private browsing? Think again. Even if you are using a secure browser, you are probably still getting tracked when you go online.
Intel 2.0's customer dilemma: the foundry move
Opinion: Hardware is Hard
5 alternatives to using WhatsApp in 2021
Quickly convert between storage size units: KB, MB, GB, TB & 512 byte blocks
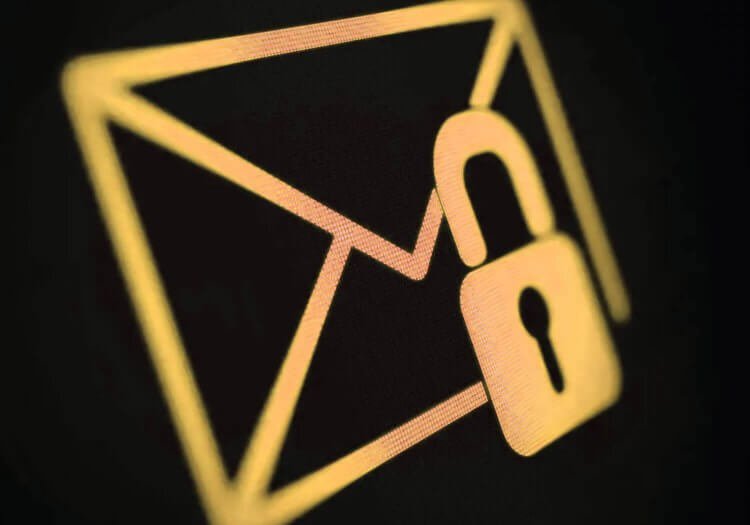
ProtonMail review: Is secure email really secure?
The best password managers
Keeping it private: 5 VPNs that have been verified to keep no logs
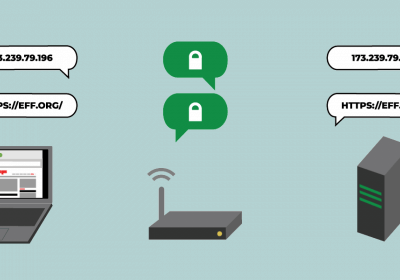
EFF: Encrypted DNS could help close the biggest privacy gap on the Internet
The Authoritative Guide to Blockchain Development
Cryptocurrencies, ICOs, magic internet money---it's all so damn exciting, and you, the eager developer, want to get in on the madness. Where do you start? I'm glad you're excited about this space. I am too. But you'll probably find it's unclear where to begin. Blockchain is moving at breakneck speed, but there's no clear onramp to learning this stuff.
How To: Taking Pictures of PCBs
I've started to develop a strange pleasure for taking pictures of PCBs and I wanted to share my experience. Sure, you can take pictures of PCBs with your smartphone and get nice results. However, if you want repeatable quality and acceptable color, you don't need to break the bank but you will need a bit more gear.
Are AR and VR only for special occasions?
The 5 highest rated games on Steam probably aren't what you expect
Of the 100 billion games on Steam, one for every star in the sky, which are the absolute cream of the crop? Which have users rated the highest? To borrow a cliche from The Bad Internet, the answer may surprise you.
When fans take their love for Twitch streamers too far
The robotic future
How I hacked my smart TV from my bed via a command injection
Full Throttle Remastered Review
Full Throttle Remastered feels like a supernova. It's bombastic, head-turning, and holds your attention during the brief time it flashes. The classic adventure game holds up today, but, unlike other Double Fine games, it doesn't benefit much from a remaster. The original was already as good as it needed to be.